Crime
Rocky Mountain House RCMP seek public assistance to locate wanted male

Rocky Mountain House, Alberta –
RCMP are seeking the public’s help in locating a male wanted in a violent home invasion on December 26, 2017.
Keehoo Rick Cardinal, age 35, of no fixed address has been charged with Robbery, Break & Enter, Pointing a Firearm and 7 additional Criminal Code charges for his alleged involvement in the Boxing Day incident.

Cardinal should be considered armed and dangerous. RCMP are asking the public not to approach and call 9-1-1 immediately should he be spotted.
If you have information about Keehoo Cardinal’s whereabouts, please call the Rocky Mountain House RCMP at 403-845-2882 or call your local police service. If you want to remain anonymous you can contact Crime Stoppers by phone at 1-800-222-8477 (TIPS), by internet at www.tipsubmit.com or by SMS.
BACKGROUND:
December 30, 2017
Rocky Mountain House RCMP make arrests in two Violent Home Invasions
Rocky Mountain House, Alberta – On December 26, 2017 around 9:15 a.m., Rocky Mountain House RCMP responded to a call for service of a home invasion at a residence in the town of Rocky Mountain House. Upon arrival, Police discovered the lone male suspect had departed. There was evidence to show three individuals in the residence were assaulted and robbed of property. At approximately 10:00 a.m., the same day, three suspects forced their way into another residence within the town of Rocky Mountain House, where the home owner was assaulted with a weapon, unlawfully confined, and robbed of property.
On December 29, 2017, Rocky Mountain House RCMP, with the assistance of the RCMP Calgary Emergency Response Team, executed two search warrants at two different residences within the town of Rocky Mountain House. Several individuals were arrested as a result. Firearms stolen from one of the home invasions were recovered, along with other offence related property. The investigation continued with the assistance of the RCMP Calgary General Investigation Section. The following three individuals have been charged with numerous Criminal Code offences connected to the two home invasions:
Rickie Wapoose CARDINAL (30) of Rocky Mountain House, has been charged with :
– Robbery X 2 – Sec. 344(b) CC
– Break and Enter X 2 – Sec. 348(1)(b) CC
– Uttering Threats X 3 – Sec. 264.1 CC
– Assault with a Weapon X 4 – Sec. 267(a) CC
– Assault X 2 – Sec. 266 CC
– Disobey a Lawful Order X 5 – Sec. 127 CC
– Extortion – Sec. 346(1.1)(a.1) CC
– Pointing a Firearm – Sec. 87 CC
– Unlawful Confinement – Sec. 279(1) CC
– Disguise with Intent – Sec. 351(2) CC
– Robbery to Steal Firearm – Sec. 98.1 CC
– Possession of a Weapon Obtained by Commission of an Offence X 3 – 96(a) CC
– Unlawful Possession of a Firearm X 3 – Sec. 92(1) CC
– Careless Storage of a Firearm – Sec. 86(1) CC
– Possession of Prohibited Weapon – Sec. 91(2) CC
Keehoo Rick CARDINAL (35) of no fixed address, and Shanel BRODERSEN (26) of Rocky Mountain House, have been charged with:
– Robbery – Sec. 344(b) CC
– Break and Enter – Sec. 348(1)(b) CC
– Extortion – Sec. 346(1.1)(a.1) CC
– Pointing a Firearm – Sec. 87 CC
– Unlawful Confinement – Sec. 279(2) CC
– Disguise with Intent – 351(2) CC
– Uttering Threats – Sec. 264.1(1) CC
– Assault with a Weapon X 2 – Sec. 267(a) CC
– Robbery to Steal a Firearm – Sec. 98.1 CC
Police have determined that all the individuals involved in these home invasions were known to one another.
Rickie Wapoose CARDINAL and Shanel BRODERSEN were remanded into police custody and will appear in Rocky Mountain House Provincial Court on Wednesday, January 3, 2018. A warrant for arrest has been sought for Keehoo CARDINAL. The Rocky Mountain House RCMP are seeking the public’s assistance in locating him. If you have information about Keehoo CARDINAL’s whereabouts, please call the Rocky Mountain House RCMP at 403-845-2882 or call your local police service. Keehoo CARDINAL is considered armed and dangerous. If you want to remain anonymous you can contact Crime Stoppers by phone at 1-800-222-8477 (TIPS), by internet at www.tipsubmit.com or by SMS.
Automotive
Dark Web Tesla Doxxers Used Widely-Popular Parking App Data To Find Targets, Analysis Shows


From the Daily Caller News Foundation
By Thomas English
A dark web doxxing website targeting Tesla owners and allies of Elon Musk appears to be compiled from hacked data originally stolen from a massive ParkMobile app breach in 2021, according to records obtained by a data privacy group.
The site, known as DogeQuest, first appeared in March and publishes names, home addresses, contact details and other personal information tied to Tesla drivers and DOGE staff. Marketed as a hub for anti-Musk “creative expressions of protest,” the platform has been linked to real-world vandalism and remains live on the dark web. Federal investigations into DogeQuest are already underway, the New York Post first reported.
“If you’re on the hunt for a Tesla to unleash your artistic flair with a spray can, just step outside — no map needed! At DOGEQUEST, we believe in empowering creative expressions of protest that you can execute from the comfort of your own home,” the surface-web DogeQuest site reads. “DOGEQUEST neither endorses nor condemns any actions.”

A screenshot of the DogeQuest surface website captured on April 3, 2025. (Captured by Thomas English/Daily Caller News Foundation)
ObscureIQ, a data privacy group, compiled a breakdown of the data — obtained by the Daily Caller News Foundation — and determined 98.2% of records used to populate the site matched individuals affected by the 2021 ParkMobile breach.
Encouraging destruction of Teslas throughout the country is extreme domestic terrorism!! https://t.co/8TCNIbrQxA
— Elon Musk (@elonmusk) March 18, 2025
DogeQuest originally appeared as a surface web doxxing hub, encouraging vandalism of Teslas and displaying names, addresses, contact details and, in some cases, employment information for roughly 1,700 individuals. The site used stolen ParkMobile records along with data purchased from brokers, flagging anyone who had a Tesla listed in their vehicle registration profile, according to ObscureIQ’s analysis.
The platform — now operating as “DogeQuest Unleashed” via a .onion dark web address — has also published personal details of high-value targets including senior military officials, federal employees and private sector executives in Silicon Valley. A spreadsheet reviewed by the Daily Caller News Foundation indicates several individuals targeted work areas like cybersecurity, defense contracting, public health and diplomatic policy. DOGE staff and their families appear prominently throughout the data.

A screenshot of DogeQuest’s surface website, captured on April 3, 2025. (Captured by Thomas English/Daily Caller News Foundation)
No other reporting has yet tied DogeQuest directly to the ParkMobile breach, which impacted over 21 million users in 2021. The company, which facilitates cashless parking across the U.S., quietly disclosed the breach in April of that year, admitting that “basic user information” had been accessed. ObscureIQ’s research shows that exposed data included email addresses, license plate numbers and phone numbers — enough to triangulate identity when paired with commercial data brokers.
The company agreed to a $32 million settlement to resolve a class-action lawsuit stemming from the data breach. The lawsuit alleged that ParkMobile failed to secure its Amazon Web Services cloud storage, allowing access to the data. Although payment data were reportedly not compromised, plaintiffs argued the exposed information still posed serious privacy risks — a claim now reinforced by its use in the DogeQuest doxxing campaign.
Despite federal attention, the site has proven difficult to keep offline, as the dark web mirror incorporates anonymized hosting methods, frustrating law enforcement takedown efforts.
The Department of Justice charged three suspects last week linked to physical attacks on Tesla vehicles, charging stations and dealerships across multiple states, though it has not publicly confirmed any link between those suspects and DogeQuest. Meanwhile, the FBI has acknowledged it is “actively working” on both the doxxing campaign and a parallel rise in swatting incidents affecting DOGE affiliates.
Crime
Europol takes out one of the largest pedophile networks in the world with almost 2 million users

From LifeSiteNews
An international group of police agencies has taken down one of the largest pedophile networks in the world with almost two million users.
Investigators from Bavaria, Germany, announced yesterday that they dismantled an online pedophile platform called “Kidflix” used to distribute child pornography that had around 1.8 million users worldwide. Police carried out raids in 31 countries and arrested 79 people in total.
The European police unit Europol coordinated the operation led by the Bavarian criminal police. Europol announced that around 1,400 suspects have been identified worldwide in “one of the biggest blows against child pornography in recent years, if not ever.”
According to Europol, the platform “Kidflix” was one of the largest pedophile networks in the world. Guido Limmer, deputy head of the Bavarian criminal police, said it was the “largest operation ever” organized by Europol. The platform’s server, with over 70,000 videos at the time, was reportedly shut down by German and Dutch authorities in early March.
The 79 people arrested were not only suspected of having watched or downloaded videos of child sexual abuse but some were also suspected of personally harming children. The police units carried out the raids from March 10 to 23 and reportedly confiscated thousands of electronic devices. In Germany alone, 96 locations were raided. Among the suspects was a 36-year-old man who not only viewed illegal material but also reportedly offered up his young son for sexual abuse. The child was given to child protection services after the man was arrested, the Bavarian police spokesman said.
Limmer also noted that one of the arrested suspects was a “serial” abuser from the United States.
According to Europol, “Kidflix” was set up by cybercriminals in 2021 and became one of the most popular platforms for pedophiles. The international police agency said that the investigation into the network began in 2022.
In October 2024, German police dismantled another large online pedophile network with hundreds of thousands of users, arresting six men associated with the platform.
Last year, Germany’s Federal Criminal Police Office revealed that the cases of sexual abuse against children and adolescents had more than tripled in the past five years.
-
 2025 Federal Election20 hours ago
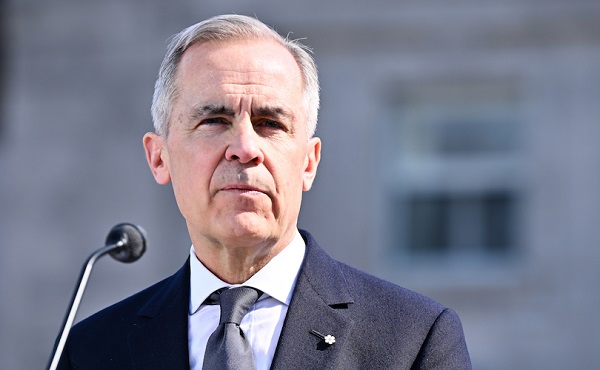
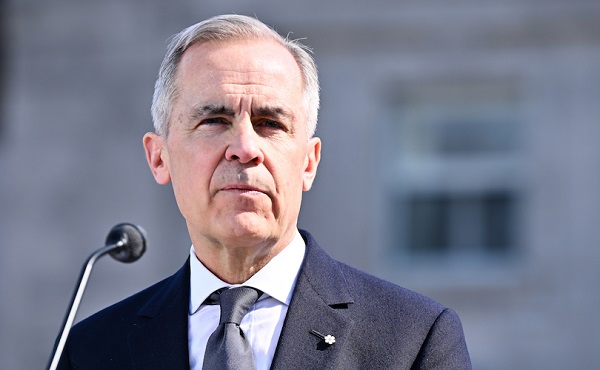
2025 Federal Election20 hours agoMark Carney refuses to clarify 2022 remarks accusing the Freedom Convoy of ‘sedition’
-

 2025 Federal Election24 hours ago
2025 Federal Election24 hours agoPoilievre To Create ‘Canada First’ National Energy Corridor
-

 Bruce Dowbiggin22 hours ago
Bruce Dowbiggin22 hours agoAre the Jays Signing Or Declining? Only Vladdy & Bo Know For Sure
-

 2025 Federal Election23 hours ago
2025 Federal Election23 hours agoFixing Canada’s immigration system should be next government’s top priority
-

 Daily Caller21 hours ago
Daily Caller21 hours agoBiden Administration Was Secretly More Involved In Ukraine Than It Let On, Investigation Reveals
-

 2025 Federal Election2 days ago
2025 Federal Election2 days agoCanada Continues to Miss LNG Opportunities: Why the World Needs Our LNG – and We’re Not Ready
-

 Health2 days ago
Health2 days agoSelective reporting on measles outbreaks is a globalist smear campaign against Trump administration.
-

 2025 Federal Election2 days ago
2025 Federal Election2 days agoMark Carney is trying to market globalism as a ‘Canadian value.’ Will it work?

