Crime
Europol takes out one of the largest pedophile networks in the world with almost 2 million users

From LifeSiteNews
An international group of police agencies has taken down one of the largest pedophile networks in the world with almost two million users.
Investigators from Bavaria, Germany, announced yesterday that they dismantled an online pedophile platform called “Kidflix” used to distribute child pornography that had around 1.8 million users worldwide. Police carried out raids in 31 countries and arrested 79 people in total.
The European police unit Europol coordinated the operation led by the Bavarian criminal police. Europol announced that around 1,400 suspects have been identified worldwide in “one of the biggest blows against child pornography in recent years, if not ever.”
According to Europol, the platform “Kidflix” was one of the largest pedophile networks in the world. Guido Limmer, deputy head of the Bavarian criminal police, said it was the “largest operation ever” organized by Europol. The platform’s server, with over 70,000 videos at the time, was reportedly shut down by German and Dutch authorities in early March.
The 79 people arrested were not only suspected of having watched or downloaded videos of child sexual abuse but some were also suspected of personally harming children. The police units carried out the raids from March 10 to 23 and reportedly confiscated thousands of electronic devices. In Germany alone, 96 locations were raided. Among the suspects was a 36-year-old man who not only viewed illegal material but also reportedly offered up his young son for sexual abuse. The child was given to child protection services after the man was arrested, the Bavarian police spokesman said.
Limmer also noted that one of the arrested suspects was a “serial” abuser from the United States.
According to Europol, “Kidflix” was set up by cybercriminals in 2021 and became one of the most popular platforms for pedophiles. The international police agency said that the investigation into the network began in 2022.
In October 2024, German police dismantled another large online pedophile network with hundreds of thousands of users, arresting six men associated with the platform.
Last year, Germany’s Federal Criminal Police Office revealed that the cases of sexual abuse against children and adolescents had more than tripled in the past five years.
2025 Federal Election
Nine Dead After SUV Plows Into Vancouver Festival Crowd, Raising Election-Eve Concerns Over Public Safety

 Sam Cooper
Sam Cooper
In Vancouver, concern about public safety — particularly assaults and violent incidents involving suspects previously known to police — has been a longstanding civic and political flashpoint
In an evolving mass-death investigation that could have profound psychological and emotional impacts on Canada’s federal election, Vancouver police confirmed Sunday that nine people were killed Saturday night when a young man plowed a luxury SUV through a festival block party in South Vancouver, leaving a trail of instant deaths and horrific injuries, with witnesses describing convulsing bodies and wounded toddlers in the aftermath.
The driver, a 30-year-old Vancouver resident known to police, appeared to be shaken and apologetic, according to eyewitness accounts and video from the scene. Authorities stated the case is not being treated as terrorism.
Late Saturday night, Vancouver police confirmed at a news conference that the man, who was known to police “in certain circumstances,” had been arrested.
The incident occurred around 8:14 p.m. during the annual Lapu Lapu Festival, a celebration of Filipino Canadian culture held near East 41st Avenue and Fraser Street. Thousands of attendees had packed the area for cultural performances, food stalls, and community events when the luxury SUV entered the closed-off area and accelerated into the crowd. Photos of the vehicle, with its doors ajar and a crumpled front end, indicate it was an Audi Q7 with black tinted windows.
In Vancouver, concern about public safety — particularly assaults and violent incidents involving suspects previously known to police — has been a longstanding civic and political flashpoint. Saturday’s tragedy sharpened those anxieties, potentially influencing the attitudes of undecided voters in a federal election that has focused on social disorder and crime framed by the Conservative side, with the Liberal frontrunners countering that firmer sentencing laws would undermine Canada’s Charter of Rights.
Witnesses to Saturday’s tragedy described scenes of chaos and terror as the SUV slammed into festival-goers, accelerating through the crowd.
“I thought it was fireworks at first — the sounds, the screams — then I saw people flying,” one witness told reporters on the scene.
Authorities have launched a full criminal investigation into the suspect’s background, including previous interactions with law enforcement.
The tragedy unfolded during the final, high-stakes weekend of Canada’s federal election campaign, throwing public safety and political leadership into sharp relief.
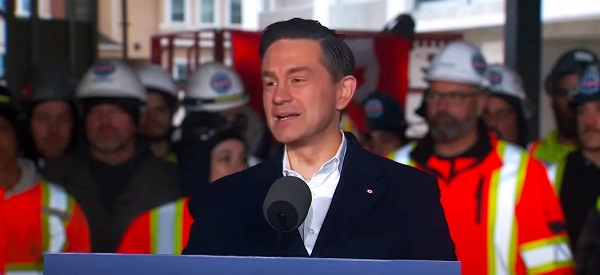
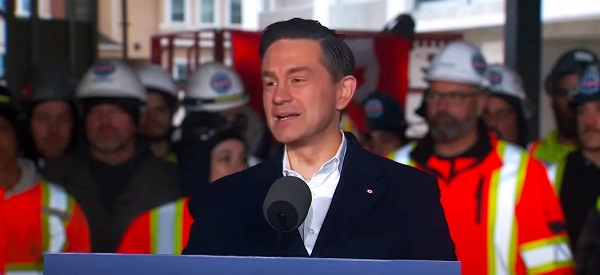
On Saturday night, before news of the Vancouver incident broke, Conservative leader Pierre Poilievre posted a message on X at about 10 p.m., declaring, “This election comes down to one word. Change. Our Conservative plan will bring home an affordable life and safe streets — For a Change.”
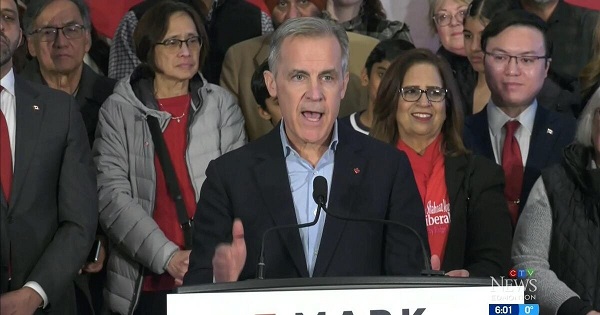
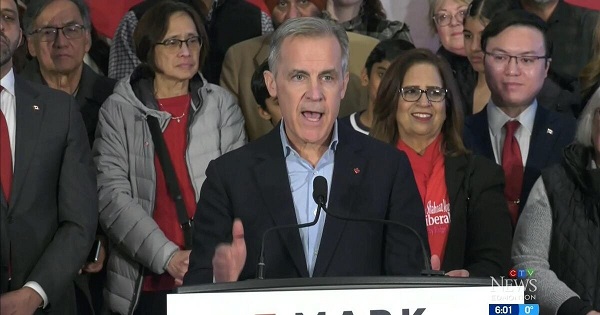
Meanwhile, Liberal leader Mark Carney, campaigning in the Greater Toronto Area, posted at roughly the same time, “Dropped in on dim sum today in Markham. The best part of this campaign has been meeting Canadians in their communities — and hearing how excited they are about our future.”
As the scale of the tragedy became clear, both leaders shifted sharply in tone.
Poilievre posted again around 1 a.m. Sunday, writing, “I am shocked by the horrific news emerging from Vancouver’s Lapu Lapu Day Festival tonight. My thoughts are with the Filipino community and all the victims targeted by this senseless attack. Thank you to the first responders who are at the scene as we wait to hear more.”
Carney, who had posted shortly before midnight that, “We don’t need anger. We need to build,” followed with a direct statement on the Vancouver attack around 2 a.m. Sunday morning, writing, “I am devastated to hear about the horrific events at the Lapu Lapu festival in Vancouver earlier this evening. I offer my deepest condolences to the loved ones of those killed and injured, to the Filipino Canadian community, and to everyone in Vancouver. We are all mourning with you.”
Online, the tragedy quickly reignited concerns about violent crime, bail, and the rights of offenders — issues that have increasingly polarized Canadian political debate.
In response to Carney’s statement, a comment from an account named Willy Balters reflected the growing anger: “He’ll be out on bail by morning right?”
Another commenter, referencing past political controversies over judicial reform, posted to Carney, “You stood behind a podium and declared murderers’ Charter Rights can’t be violated.”
The raw public sentiment mirrored broader criticisms that Canada’s criminal justice system — and its perceived leniency toward repeat offenders — has failed to keep Canadians safe.
Just days prior, a different incident tapped into similar public anger. B.C. Conservative MLA Elenore Sturko posted, “A visitor to Vancouver was brutally attacked by a man only hours after he was released on bail for assaulting police and uttering threats. @Dave_Eby — is this the kind of welcome visitors to FIFA will have to look forward to? BTW, this violent man is out on bail AGAIN!”
That incident continued to draw heated social media on Sunday, with David Jacobs, a well-known conservative-leaning commenter, posting, “A man, while out on bail for assaulting a peace officer, violently assaulted a woman. He’s out on bail again. The Liberals put criminal rights far ahead of victim rights and community safety. Stop the insanity. Vote for change!”
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
Invite your friends and earn rewards
2025 Federal Election
Police Associations Endorse Conservatives. Poilievre Will Shut Down Tent Cities

From Conservative Party Communications
Under the Lost Liberal decade, homelessness has surged by 20% since 2018 and chronic homelessness has spiked 38%. In cities like Nanaimo, Victoria and London, the number of people living in tents and makeshift shelters has exploded. In Toronto alone, there were 82 encampments in early 2023—now there are over 200, with an estimated 1,400 in Ontario.
Yesterday, Conservative Leader Pierre Poilievre received the endorsement of the Toronto Police Association, the largest single association of its kind in Canada, representing approximately 8,000 civilian and uniformed members.
This follows the endorsement by the police associations of Durham, Peel, Barrie, and Sault Ste. Marie of the Conservative plan to stop the crime and keep Canadians safe, after the Liberal government’s easy bail and soft-on-crime policies unleashed a wave of violent crime.
“These men and women put their lives on the line every day to keep our streets safe,” Poilievre said. “Our Conservative team is honoured to have their support and will back them up with laws to help them protect all Canadians.”
Poilievre also announced that a new Conservative government will ensure that police have the legal power to remove dangerous encampments to end the homelessness and the mental health and addiction crisis that has trapped thousands in dangerous tent cities and make life unsafe for law-abiding Canadians who live near them.
“Parks where children played are now littered with needles. Small businesses are boarded up and whole blocks of storefronts are shuttered because their owners can’t afford to deal with constant break-ins and vandalism,” Pierre Poilievre said. “Public spaces belong to everyone, but law-abiding citizens, especially families and seniors, are being pushed out to accommodate chaos and violence.”
Canadian cities have a mixed record of dealing with encampments in public places, with some not acting because they don’t believe they have the legal authority to remove the camps. Conservatives will work with provinces and ensure law enforcement has the clear legal tools they need to remove encampments and give Canadians back the safe streets and public spaces they deserve.
A Poilievre-led government will do this by reversing the Liberals’ radical pro-drug policies and by:
- Amending the Criminal Code to give police the tools to charge individuals when they endanger public safety or discourage the public from using, moving through, or otherwise accessing public spaces by setting up temporary structures, including tents.
- Clarifying in law that police can dismantle illegal encampments and ensure individuals living in them who need help are connected with housing, addiction treatment, and mental health services.
- Giving judges the power to order people charged for illegally occupying public spaces with a temporary structure and simple possession of illegal drugs to mandatory drug treatment.
- Returning to a housing first approach to homelessness, ensuring people get off the streets into a stable place to live with the support they need to rebuild their lives.
Under the Lost Liberal decade, homelessness has surged by 20% since 2018 and chronic homelessness has spiked 38%. In cities like Nanaimo, Victoria and London, the number of people living in tents and makeshift shelters has exploded. In Toronto alone, there were 82 encampments in early 2023—now there are over 200, with an estimated 1,400 in Ontario.
These encampments are a direct result of radical Liberal policies such as drug decriminalization and unsafe supply. They are extremely dangerous for the people trapped in them, who endure overdoses, assaults, including sexual assaults, human trafficking, and even homicide, as well as the community around them.
Under the Poilievre plan, tent cities will no longer be an option—but recovery will be. Conservatives will give law enforcement the tools they need to help clean up our streets, deal with chronic offenders, and provide truly compassionate recovery and treatment where it is needed.
“Instead of getting people the help they need, the Liberals abandoned our communities to chaos,” Poilievre said. “Leaving people trapped by their addictions to live outdoors through Canadian winters, sick, malnourished, cold, wet and vulnerable is the furthest thing from compassionate.”
A Conservative government will also overhaul the Liberals’ dangerous pro-drug policies that have led to over 50,000 overdose deaths over the Lost Liberal Decade. Instead of flooding our streets with taxpayer-funded hard drugs, we will invest in recovery to break the cycle of despair and offer real hope.
Conservatives will allow judges to sentence offenders to mandatory treatment for addiction, and we will fund 50,000 addiction treatment spaces, ensuring that those struggling with substance use get the support they need to recover—because real compassion means helping people get better, not enabling their suffering.
In addition to these measures, Poilievre has a plan to end the soft-on-crime approach of the Lost Liberal Decade, end the chaos, and restore order and safety across Canada:
- Three-Strikes-and-You’re-Out Law: Individuals convicted of three serious offences will face a minimum prison term of 10 years and up to a life sentence, with no eligibility for bail, probation, parole, or house arrest.
- Mandatory Life Sentences: Life imprisonment for those convicted of five or more counts of human trafficking, importing or exporting ten or more illegal firearms, or trafficking fentanyl.
- Repeal of Bill C-75: Ending the Liberals’ catch-and-release policies to restore jail, not bail, for repeat violent offenders.
- New Offense for Intimate Partner Assault: Creation of a specific offense for assault of an intimate partner, with the strictest bail conditions for those accused, and ensuring that murder of an intimate partner, one’s own child, or a partner’s child is treated as first-degree murder.
- Consecutive Sentences for Repeat Violent Offenders: So there will no longer be sentencing discounts for multiple murderers.
Canadians can’t afford a fourth Liberal term of rising crime and chaos in our streets. We need a new Conservative government that will end the chaos, restore order on our streets and bring our loved ones home drug-free.
-

 2025 Federal Election1 day ago
2025 Federal Election1 day agoThe Federal Brief That Should Sink Carney
-
 2025 Federal Election1 day ago
2025 Federal Election1 day agoHow Canada’s Mainstream Media Lost the Public Trust
-

 2025 Federal Election1 day ago
2025 Federal Election1 day agoOttawa Confirms China interfering with 2025 federal election: Beijing Seeks to Block Joe Tay’s Election
-
 2025 Federal Election1 day ago
2025 Federal Election1 day agoReal Homes vs. Modular Shoeboxes: The Housing Battle Between Poilievre and Carney
-

 Media10 hours ago
Media10 hours agoCBC retracts false claims about residential schools after accusing Rebel News of ‘misinformation’
-
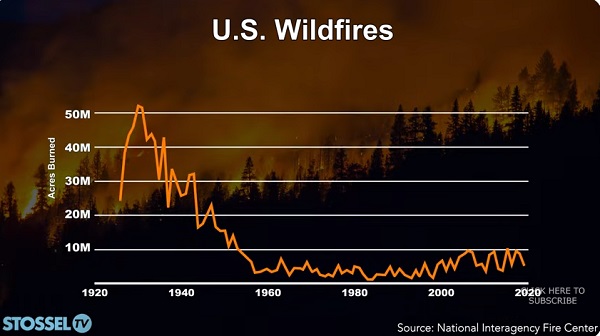
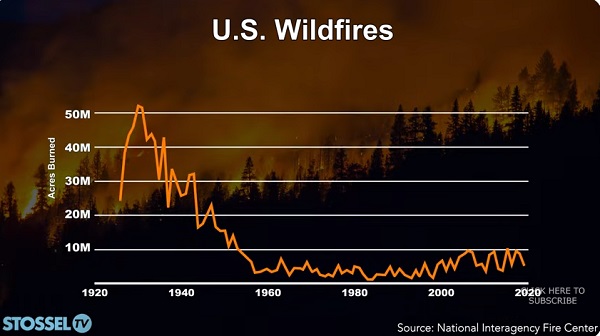 John Stossel1 day ago
John Stossel1 day agoClimate Change Myths Part 2: Wildfires, Drought, Rising Sea Level, and Coral Reefs
-

 COVID-191 day ago
COVID-191 day agoNearly Half of “COVID-19 Deaths” Were Not Due to COVID-19 – Scientific Reports Journal
-
 Bjorn Lomborg9 hours ago
Bjorn Lomborg9 hours agoNet zero’s cost-benefit ratio is CRAZY high


