Censorship Industrial Complex
Chinese firms show off latest police-state surveillance tech at security expo

From LifeSiteNews
By Angeline Tan
45 Chinese firms have showcased their latest police-state products and technologies, with one expert warning that the communist nation is doing so to normalize their method of surveillance and have it adopted abroad.
45 Chinese firms have showcased their latest police-state products and technologies, including state-of-the-art CCTV, precise DNA-testing technology and intrusive facial tracking software, at the inaugural Public Security Tech Expo in Lianyungang, located in China’s Jiangsu province.
Hosted by China’s First Research Institute of the Ministry of Public Security, the 6-day tech expo which began on September 7 showed off advanced technologies in the domains of “criminal technology, police protective equipment, traffic management equipment, anti-terrorism rescue, and command and communication,” according to the forum’s website.
The website’s official description says “the main purpose of holding the Public Security Tech Expo (Lianyungang) under the framework of the Forum is to deepen technical exchanges and international cooperation in the field of public security science and technology equipment, share useful experience in the application of science and technology equipment to public security practice, and jointly improve the ability and level of maintaining public security.”
One firm participating in the expo, Caltta Technologies, featured a project aimed at “helping” the southern African nation of Mozambique establish an “Incident Response Platform,” extolling its abilities to harness data in “rapid target location.”
Tech giant Huawei was also at the expo, boasting that its “Public Safety Solution” is currently used in more than 100 countries and regions, from Kenya to Saudi Arabia. The United States sanctioned Huawei in 2019, castigating the firm as “an arm” of the Chinese surveillance state.
The expo also saw China’s Ministry of Public Security’s Institute of Forensic Science show off its new high-tech DNA testing technologies. In 2020, Washington banned the institute from accessing some U.S. technology after a number of Chinese firms decried the institute as being “complicit in human rights violations and abuses.”
In 2018, the U.S. Treasury stated that residents of Xinjiang “were required to download a desktop version” of the app “so authorities could monitor for illicit activity.”
Communist China has been slammed for jailing over one million Uyghurs and other Muslim minorities in Xinjiang – claims Beijing vehemently denies. Nonetheless, critics have pointed out how China’s surveillance technologies have been used to draconically suppress dissidents in the Xinjiang province.
During the expo’s opening ceremony, China’s police minister praised Beijing for training thousands of overseas police officers this past year – and pledged to aid in the training of thousands more over the coming year.
Reacting to these disturbing developments, especially China’s activity abroad, Bethany Allen at the Australian Strategic Policy Institute said, “Beijing is hoping to normalize and legitimize its policing style and… the authoritarian political system in which it operates.”
According to UCA News, “China is one of the most surveilled societies on Earth, with millions of CCTV cameras scattered across cities and facial recognition technology widely used in everything from day-to-day law enforcement to political repression.”
The same UCA News article added:
Its police serve a dual purpose: keeping the peace and cracking down on petty crime while also ensuring challenges to the ruling Communist Party are swiftly stamped out.
Notably, various foreign police officers said they hoped to use Chinese surveillance technology to police their own countries.
“We can learn from China,” said Sydney Gabela, a major general in the South African police service, according to UCA News.
“We wanted to check out the new technologies that are coming out so that we can deploy them in South Africa,” Gabela said.
China’s notoriety for being a highly-surveilled state goes back a long way. In 2023, The Economist ran an article detailing how the prevalence of CCTV cameras in Communist China, many bedecked with facial-recognition technology, “leave criminals with nowhere to hide.” A September 2019 report by the U.S. Commission on International Religious Freedom (USCIRF) also disclosed that “the Chinese government has increasingly employed advanced technology to amplify its repression of religious and faith communities.”
The executive summary of the same USCIRF report stated:
Authorities have installed surveillance cameras both outside and inside houses of worship to monitor and identify attendees. The government has deployed facial recognition systems that are purportedly able to distinguish Uighurs and Tibetans from other ethnic groups. Chinese authorities have also collected biometric information—including blood samples, voice recordings, and fingerprints—from religious and faith communities, often without their consent. The government uses advanced computing platforms and artificial intelligence to collate and recognize patterns in the data on religious and faith communities. Chinese technology companies have aided the government’s crackdown on religion and belief by supplying advanced hardware and computing systems to government agencies.
Censorship Industrial Complex
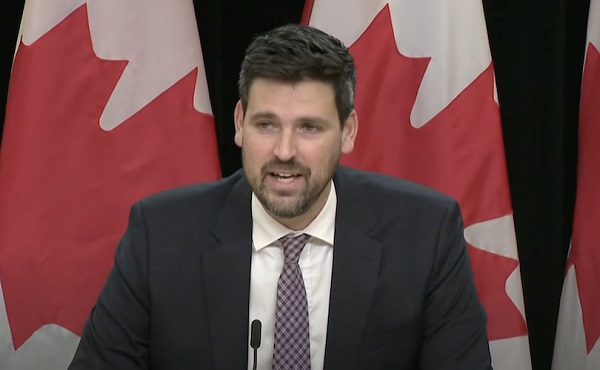
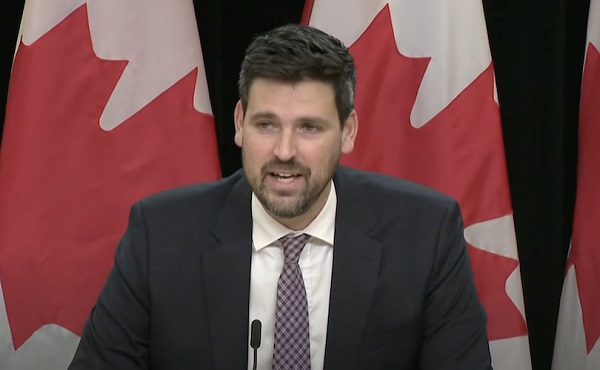
Canada’s justice minister confirms ‘hate crimes’ bill applies to online content
From LifeSiteNews
Individuals could be criminally charged for social media posts or other online content deemed offensive by the government under the Combating Hate Act.
Canadian Justice Minister Sean Fraser admitted that his new “hate crime” bill would indeed allow a person to be criminally charged for social media posts deemed offensive by the government.
Recently asked about Bill C-9, the Combating Hate Act, Fraser said the bill would indeed apply to certain online content that involves the “willful promotion of hatred.”
“Generally speaking, the law will apply equally online as it does in real communities,” he said, adding, “just in the limited circumstances where there is the willful promotion of hatred against someone.”
As reported by LifeSiteNews, Bill C-9 has been blasted by constitutional experts as allowing empowered police and the government to go after those it deems have violated a person’s “feelings” in a “hateful” way.
Bill C-9 was brought forth in the House of Commons on September 19 by Fraser. The Liberals have boasted that the bill will make it a crime for people to block the entrance to, or intimidate people from attending, a church or other place of worship, a school, or a community center. The bill would also make it a crime to promote so-called hate symbols and would, in effect, ban the display of certain symbols such as the Nazi flag.
While being questioned by Conservative MP Andrew Lawton about Bill C-9, Fraser was asked if the new law would “affect what people can say and write on the internet” and also if people could be retroactively punished for online comments made today.
In reply, Fraser said, “The only circumstance where you could imagine some online comment attracting scrutiny under this law would attach to behaviour that is criminal today but would be punished less severely.”
He said that “(t)he willful promotion of hate is a crime today, but we want to recognize a distinct charge where that same behaviour uses certain symbols of hate to bring a higher degree of culpability.”
John Carpay of the Justice Centre for Constitutional Freedoms (JCCF) has blasted Bill C-9 as something that would “empower police” and the government to go after those it deems have violated a person’s “feelings” in a “hateful” way.
Also, as reported by LifeSiteNews, Conservative MP Leslyn Lewis called out the hypocrisy of Bill C-9 for being silent regarding rising “Christian hate.”
Lewis has warned before that Bill C-9 will open the door for authorities to prosecute Canadians’ speech deemed “hateful possibly.”
Carpay also lamented how the bill mentions “rising antisemitism” but says nothing about the arson attacks on Catholic and Christian churches plaguing Canada.
“Anti-Catholic hate is obviously not on the minister’s radar. If it were, he would have mentioned it when introducing the Combating Hate Act,” Carpay wrote.
Since taking power in 2015, the Liberal government has introduced numerous new bills that, in effect, censor internet content and restrict people’s ability to express their views.
Censorship Industrial Complex
Who tries to silence free speech? Apparently who ever is in power.
Now that Trump is running Washington, Conservative thinkers must ponder a new-found appreciation for silencing speech they don’t like.
From StosselTV
War on Words: Both Parties Try to Silence Speech They Don’t Like
Donald Trump, before he was reelected, said he’d end government censorship. But now that he’s in office? He calls speech he doesn’t like “illegal.”
Free Speech should be a bedrock American value, no matter who’s in office. After the murder of Charlie Kirk, Republicans, who once complained about censorship, became censors. Democrats suddenly flip-flopped. All politicians should remember, the way to fight speech you don’t like, is with more speech, not censorship.
After 40+ years of reporting, I now understand the importance of limited government and personal freedom.
——————————————
Libertarian journalist John Stossel created Stossel TV to explain liberty and free markets to young people.
Prior to Stossel TV he hosted a show on Fox Business and co-anchored ABC’s primetime newsmagazine show, 20/20.
Stossel’s economic programs have been adapted into teaching kits by a non-profit organization, “Stossel in the Classroom.” High school teachers in American public schools now use the videos to help educate their students on economics and economic freedom. They are seen by more than 12 million students every year.
———
To make sure you receive the weekly video from Stossel TV, sign up here: https://www.johnstossel.com/#subscrib…
———
-
 Agriculture1 day ago
Agriculture1 day agoFrom Underdog to Top Broodmare
-

 Health1 day ago
Health1 day agoCanada surrenders control of future health crises to WHO with ‘pandemic agreement’: report
-
 Censorship Industrial Complex1 day ago
Censorship Industrial Complex1 day agoCanada’s justice minister confirms ‘hate crimes’ bill applies to online content
-

 Health1 day ago
Health1 day agoSovereignty at Stake: Why Parliament Must Review Treaties Before They’re Signed
-

 Carbon Tax2 days ago
Carbon Tax2 days agoBack Door Carbon Tax: Goal Of Climate Lawfare Movement To Drive Up Price Of Energy
-

 Digital ID2 days ago
Digital ID2 days agoThousands protest UK government’s plans to introduce mandatory digital IDs
-

 Bruce Dowbiggin1 day ago
Bruce Dowbiggin1 day agoIs The Latest Tiger Woods’ Injury Also A Death Knell For PGA Champions Golf?
-

 Business1 day ago
Business1 day ago$15B and No Guarantees? Stellantis Deal explained by former Conservative Shadow Minister of Innovation, Science and Technology









