Censorship Industrial Complex
Betting Site CEO Slams FBI Raid and Device Seizures As Politically Driven After Site Correctly Calls Trump’s Election Win

|
Early Wednesday morning, Shayne Coplan, CEO of the betting platform Polymarket, which has been popular for election betting, was awakened by a dramatic FBI raid on his Soho apartment. This event occurred shortly after the platform had accurately predicted Donald Trump’s overwhelming win in the recent election, according to The Post.
At around 6 a.m., federal agents demanded that Coplan hand over his phone and other electronics. Critics have called the raid an unnecessary display of force, meant to intimidate and influence public perception for political ends. A close source expressed frustration, stating, “They could have asked his lawyer for any of these things. Instead, they staged a so-called raid so they can leak it to the media and use it for obvious political reasons.” Coplan himself commented on the incident, expressing his disappointment with what he perceives as a politically motivated action by the Biden administration. “It’s discouraging that the current administration would seek a last-ditch effort to go after companies they deem to be associated with political opponents. We are deeply committed to being non-partisan, and today is no different, but the incumbents should do some self-reflecting and recognize that taking a more pro-business, pro-startup approach may be what would have changed their fate this election,” he stated. |
 |
|
He also highlighted Polymarket’s role in the election, serving tens of millions without causing harm, and reaffirmed his optimism about the future of American entrepreneurship.
No official reason has been provided for the raid, but the source, and Coplan himself, suspects political motives, particularly given Polymarket’s successful forecast of Trump’s victory over Vice President Kamala Harris, contrary to most traditional polls. |
Censorship Industrial Complex
China announces “improvements” to social credit system

 MxM News
MxM News
Quick Hit:
Beijing released new guidelines Monday to revamp its social credit system, promising stronger information controls while deepening the system’s reach across China’s economy and society. Critics say the move reinforces the Communist Party’s grip under the banner of “market efficiency.”
Key Details:
- The guideline was issued by top Chinese government and Communist Party offices, listing 23 measures to expand and standardize the social credit system.
- It aims to integrate the credit system across all sectors of China’s economy to support what Beijing calls “high-quality development.”
- Officials claim the new framework will respect information security and individual rights—despite growing global concerns over surveillance and state overreach.
Diving Deeper:
China is doubling down on its social credit system with a newly issued guideline meant to “improve” and expand the controversial surveillance-driven program. Released by both the Communist Party’s Central Committee and the State Council, the document outlines 23 specific measures aimed at building a unified national credit system that will touch nearly every corner of Chinese society.
Framed as a tool for “high-quality development,” the guideline declares that credit assessments will increasingly shape the rules of engagement for businesses, government agencies, and individual citizens. The system, according to the National Development and Reform Commission (NDRC), has already played a role in shaping China’s financial services, government efficiency, and business environment.
Critics of the social credit system have long warned that it serves as an instrument of authoritarian control—monitoring citizens’ behavior, punishing dissent, and rewarding obedience to the Communist Party. By integrating credit data across all sectors and enforcing a “shared benefits” model, the new guideline appears to entrench, not ease, the Party’s involvement in everyday life.
Still, Beijing is attempting to temper foreign and domestic concerns over privacy. The NDRC emphasized that the system is being built on the “fundamental principle” of protecting personal data. Officials pledged to avoid excessive data collection and crack down on any unlawful use of information.
Censorship Industrial Complex
France condemned for barring populist leader Marine Le Pen from 2027 election

From LifeSiteNews
By Frank Wright
It remains to be seen how long the rule of lawfare can last against the rising demand for popular politics. The globalist remnants across the West are now liberal democracies in name only.
Marine Le Pen, the former leader of the populist French opposition party, has been sentenced to prison and barred from standing for election as president in 2027, following a court ruling against her for alleged financial crimes.
Le Pen is currently leading polls to win the presidential election, being 11 to 17 points ahead of the party of the globalist President Emmanuel Macron.
The ruling Monday on charges of “misuse of EU funds” sees Le Pen, leader of the National Rally (RN) party, facing two years’ imprisonment and a five-year ban on running for elected office. Her lawyer stated she would appeal the ruling.
Speaking a day before the verdict, Le Pen said, “There are 11 million people who voted for the movement I represent. So tomorrow, potentially, millions and millions of French people would see themselves deprived of their candidate in the election.”
She is to address the French nation in a televised statement Monday night.
Party leader Jordan Bardella responded on X, saying, “Today, it is not only Marine Le Pen who is unjustly condemned: it is French democracy that is being executed.”
Bardella has called for “peaceful mobilization” in support of Marine Le Pen, with a petition launched in protest at the “democratic scandal” of her effective cancellation as a candidate.
The RN won 33 percent of the vote in the first round of the 2024 French parliamentary elections, being the single largest party overall. It is prevented from entering government by a “cordon sanitaire” – an agreement between liberal-global and left-wing parties to “firewall” national-populists from power regardless of how many people vote for them.
The same system prevents Germany’s AfD and Austria’s FPO from governing. The AfD won 25 percent of the national vote, and the FPO came first in the Austrian elections – both held last year. More recently, Romanian presidential candidate Calin Georgescu saw his victorious presidential election canceled and him barred from running again, in what was described as a “globalist coup.”
Le Pen’s appeal would suspend the jail sentence and the fine of 100,000 euros – but would not be heard until 2026, effectively sabotaging her preparations for the 2027 election should she win. The ban takes effect when the appeal process is exhausted, meaning Le Pen is free to campaign until her appeal is heard in a year’s time.
The court ruled that Le Pen, whose RN was the single largest party in the recent French parliamentary elections, had misused 3 million euros in EU funds by paying party officials based in France.
She had told France’s La Tribune Dimanche on Saturday that “the judges have the power of life or death over our movement.”
The judges appear to have given her party a death sentence. Eight further RN members and twelve assistants were also found guilty in the same trial.
Elon Musk has warned the move will “backfire,” with globalist house magazine The Economist in agreement that “her sentence for corrupt use of EU funds could strengthen the hard right.” Its report stated, “Barring Marine Le Pen is a political earthquake for France.”
The shockwaves have reached across Europe, and around the world. Italy’s Deputy Prime Minister Matteo Salvini called the court’s ruling a “declaration of war by Brussels,” joining Dutch and Hungarian national-populist leaders Geert Wilders and Viktor Orban in condemnation of the move.
According to commentators, the legal ruling shows that the liberal-global regime is now canceling democracy. Independent journalist Michael Shellenberger said on X of worldwide globalist moves to criminalize its opponents: “This is a five alarm fire.”
Citing the lawfare undertaken against then-candidate Donald Trump, former State Department official Mike Benz described the many examples of the rule of lawfare were “a dagger in the heart of democracy”:
Donald Trump Jr. asked whether the French judiciary are “just trying to prove JD Vance was right” – referring to the vice president’s “blistering attack on European leaders” over their rising censorship and anti-democratic moves. Vance told EU and UK leaders in Munich, “Democracy rests on the sacred principle that the voice of the people matters. There is no room for firewalls. You either uphold the principle or you don’t.”
U.S. political strategist Steve Bannon also referenced populist figures facing legal persecution in his “War Room” rundown of the Le Pen affair today:
The move to legally “firewall” Le Pen has left even her political opponents disturbed, with the ruling Prime Minister Francois Bayrou reportedly “disquieted” by the verdict. Jean-Luc Melenchon, the leader of the left-liberal LFI and a determined political enemy of Le Pen, has said, “The decision to remove an elected official should be up to the people” – not the courts.
Right-populist leader Eric Zemmour, who coined the term “remigration,” warned of a “coup d’etat” of activist judges in 1997 – and said today that “everything has to change” as “it is not for judges to decide for whom the people must vote.”
Laurent Wauquiez of the conservative Les Republicains – who have also refused to work with the RN in coalition – said, “The decision to condemn Marine Le Pen is heavy and exceptional. In a democracy, it is unhealthy that an elected official be forbidden to stand for election.”
It seems this latest example of liberal-global lawfare may even see Le Pen’s party rise in the polls, with a survey today showing two-thirds of all French voters saying her ineligibility would not stop them voting for her RN party.
Nearly half of voters believe she was treated harshly “for political reasons,” with a quarter believing the move to bar her will be a “trump card” for the party overall.
Whether the move “backfires” or not, the message to Western electorates is becoming clear. You can vote for liberals of the left, right, or center – because anyone offering a real alternative will be locked out of power, or locked up in jail.
It remains to be seen how long the rule of lawfare can last against the rising demand for popular politics. After canceled elections, speech crackdowns, and criminalizing their opponents, the globalist remnants across the West are now liberal democracies in name only.
-

 Alberta12 hours ago
Alberta12 hours agoProvince introducing “Patient-Focused Funding Model” to fund acute care in Alberta
-

 Podcasts15 hours ago
Podcasts15 hours agoThe world is changing – Trump’s Tariffs, the US, Canada, and the rest of the world
-

 Alberta2 days ago
Alberta2 days agoIs Canada’s Federation Fair?
-

 2025 Federal Election1 day ago
2025 Federal Election1 day agoPierre Poilievre Declares War on Red Tape and Liberal Decay in Osoyoos
-

 Business1 day ago
Business1 day agoJury verdict against oil industry worries critics, could drive up energy costs
-

 2025 Federal Election14 hours ago
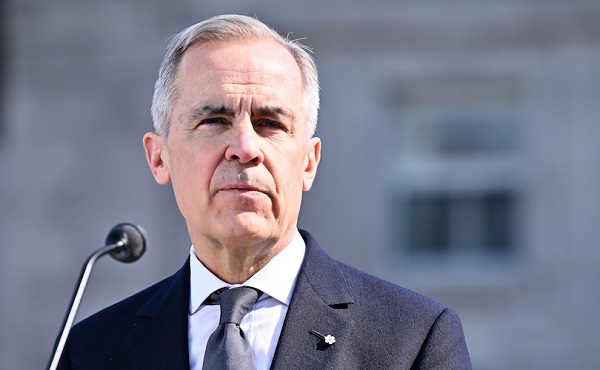
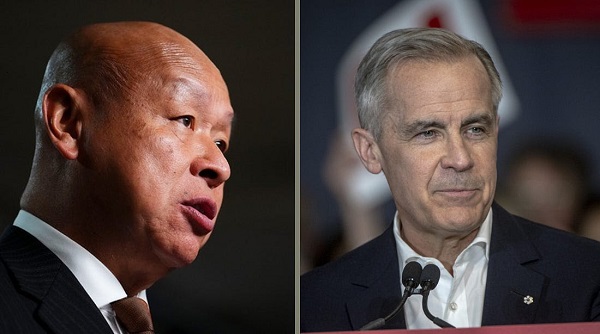
2025 Federal Election14 hours agoMark Carney Comes to B.C. and Delivers a Masterclass in Liberal Arrogance
-

 2025 Federal Election14 hours ago
2025 Federal Election14 hours agoPoilievre to invest in recovery, cut off federal funding for opioids and defund drug dens
-

 2025 Federal Election2 days ago
2025 Federal Election2 days agoLiberals Replace Candidate Embroiled in Election Interference Scandal with Board Member of School Flagged in Canada’s Election Interference Inquiry