Crime
Drumheller RCMP apprehends male following two armed robberies

Drumheller RCMP apprehends male following two armed robberies
Drumheller, Alberta – Drumheller RCMP received a report October 31st around 3:50 in the afternoon that a victim was approached by a male with long dark hair and a pitchfork. The suspect then produced a knife and demanded the victims wallet. The victim refused and left the area. Police located the suspect and arrested a 26 year old Phillipino male. Following the arrest, another report came forward that the same suspect had pointed the pitchfork at a separate victim and stated that he was robbing the victim. Neither victim was injured in the incidents.
The suspect will be appearing before a Justice for a Bail Hearing this morning. No name is released at this time pending the swearing of charges.
If anyone has information regarding these incidents or suspect, they are asked to contact the Drumheller RCMP Detachment at 403-823-7590 or their local police. If you wish to remain anonymous, you can contact Crime Stoppers at 1-800-222-8477 (TIPS), online at www.P3Tips.com or by using the “P3 Tips” app available through the Apple App or Google Play Store.”
November 1, 2018
Suspect apprehended following flight from police
Drumheller, Alberta – Drumheller RCMP apprehended a male following a report of a theft from the Carbon store. The suspect left the area in a white Kia compact car. Police located the vehicle and attempted to stop it at which time the suspect attempted to evade police, driving in a manner that was dangerous to other motorists. Police did not pursue the suspect but, with assistance from the public, were able to locate the suspect vehicle in a rural area. The suspect continued his attempt to evade police, striking a fence and ditch in the process. The suspect fled on foot into a near by coulee at which time a Police Service dog attended. The suspect was located a short distance from the vehicle suffering from serious injuries sustained during the collision with the ditch. The suspect was intoxicated and the vehicle was found to have been stolen from Okotoks. The male suspect had outstanding arrest warrants from High River and pending charges from an incident the previous night in which he stole a separate vehicle.
Due to his injuries, the suspect was taken to hospital for assessment. The suspect suffered serious, non-life threatening injuries and was released to the care of the hospital with a court date for January 2019 for charges including possession of property obtained by crime, dangerous driving and flight from police.
If anyone has information regarding this incident or suspect, they are asked to contact the Drumheller RCMP Detachment at 403-823-7590 or their local police. If you wish to remain anonymous, you can contact Crime Stoppers at 1-800-222-8477 (TIPS), online at www.P3Tips.com or by using the “P3 Tips” app available through the Apple App or Google Play Store.”
2025 Federal Election
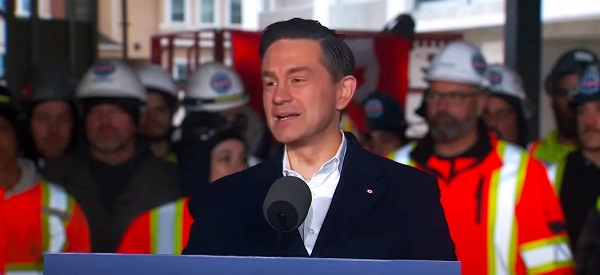
Police Associations Endorse Conservatives. Poilievre Will Shut Down Tent Cities

From Conservative Party Communications
Under the Lost Liberal decade, homelessness has surged by 20% since 2018 and chronic homelessness has spiked 38%. In cities like Nanaimo, Victoria and London, the number of people living in tents and makeshift shelters has exploded. In Toronto alone, there were 82 encampments in early 2023—now there are over 200, with an estimated 1,400 in Ontario.
Yesterday, Conservative Leader Pierre Poilievre received the endorsement of the Toronto Police Association, the largest single association of its kind in Canada, representing approximately 8,000 civilian and uniformed members.
This follows the endorsement by the police associations of Durham, Peel, Barrie, and Sault Ste. Marie of the Conservative plan to stop the crime and keep Canadians safe, after the Liberal government’s easy bail and soft-on-crime policies unleashed a wave of violent crime.
“These men and women put their lives on the line every day to keep our streets safe,” Poilievre said. “Our Conservative team is honoured to have their support and will back them up with laws to help them protect all Canadians.”
Poilievre also announced that a new Conservative government will ensure that police have the legal power to remove dangerous encampments to end the homelessness and the mental health and addiction crisis that has trapped thousands in dangerous tent cities and make life unsafe for law-abiding Canadians who live near them.
“Parks where children played are now littered with needles. Small businesses are boarded up and whole blocks of storefronts are shuttered because their owners can’t afford to deal with constant break-ins and vandalism,” Pierre Poilievre said. “Public spaces belong to everyone, but law-abiding citizens, especially families and seniors, are being pushed out to accommodate chaos and violence.”
Canadian cities have a mixed record of dealing with encampments in public places, with some not acting because they don’t believe they have the legal authority to remove the camps. Conservatives will work with provinces and ensure law enforcement has the clear legal tools they need to remove encampments and give Canadians back the safe streets and public spaces they deserve.
A Poilievre-led government will do this by reversing the Liberals’ radical pro-drug policies and by:
- Amending the Criminal Code to give police the tools to charge individuals when they endanger public safety or discourage the public from using, moving through, or otherwise accessing public spaces by setting up temporary structures, including tents.
- Clarifying in law that police can dismantle illegal encampments and ensure individuals living in them who need help are connected with housing, addiction treatment, and mental health services.
- Giving judges the power to order people charged for illegally occupying public spaces with a temporary structure and simple possession of illegal drugs to mandatory drug treatment.
- Returning to a housing first approach to homelessness, ensuring people get off the streets into a stable place to live with the support they need to rebuild their lives.
Under the Lost Liberal decade, homelessness has surged by 20% since 2018 and chronic homelessness has spiked 38%. In cities like Nanaimo, Victoria and London, the number of people living in tents and makeshift shelters has exploded. In Toronto alone, there were 82 encampments in early 2023—now there are over 200, with an estimated 1,400 in Ontario.
These encampments are a direct result of radical Liberal policies such as drug decriminalization and unsafe supply. They are extremely dangerous for the people trapped in them, who endure overdoses, assaults, including sexual assaults, human trafficking, and even homicide, as well as the community around them.
Under the Poilievre plan, tent cities will no longer be an option—but recovery will be. Conservatives will give law enforcement the tools they need to help clean up our streets, deal with chronic offenders, and provide truly compassionate recovery and treatment where it is needed.
“Instead of getting people the help they need, the Liberals abandoned our communities to chaos,” Poilievre said. “Leaving people trapped by their addictions to live outdoors through Canadian winters, sick, malnourished, cold, wet and vulnerable is the furthest thing from compassionate.”
A Conservative government will also overhaul the Liberals’ dangerous pro-drug policies that have led to over 50,000 overdose deaths over the Lost Liberal Decade. Instead of flooding our streets with taxpayer-funded hard drugs, we will invest in recovery to break the cycle of despair and offer real hope.
Conservatives will allow judges to sentence offenders to mandatory treatment for addiction, and we will fund 50,000 addiction treatment spaces, ensuring that those struggling with substance use get the support they need to recover—because real compassion means helping people get better, not enabling their suffering.
In addition to these measures, Poilievre has a plan to end the soft-on-crime approach of the Lost Liberal Decade, end the chaos, and restore order and safety across Canada:
- Three-Strikes-and-You’re-Out Law: Individuals convicted of three serious offences will face a minimum prison term of 10 years and up to a life sentence, with no eligibility for bail, probation, parole, or house arrest.
- Mandatory Life Sentences: Life imprisonment for those convicted of five or more counts of human trafficking, importing or exporting ten or more illegal firearms, or trafficking fentanyl.
- Repeal of Bill C-75: Ending the Liberals’ catch-and-release policies to restore jail, not bail, for repeat violent offenders.
- New Offense for Intimate Partner Assault: Creation of a specific offense for assault of an intimate partner, with the strictest bail conditions for those accused, and ensuring that murder of an intimate partner, one’s own child, or a partner’s child is treated as first-degree murder.
- Consecutive Sentences for Repeat Violent Offenders: So there will no longer be sentencing discounts for multiple murderers.
Canadians can’t afford a fourth Liberal term of rising crime and chaos in our streets. We need a new Conservative government that will end the chaos, restore order on our streets and bring our loved ones home drug-free.
Business
China, Mexico, Canada Flagged in $1.4 Billion Fentanyl Trade by U.S. Financial Watchdog
 Sam Cooper
Sam Cooper
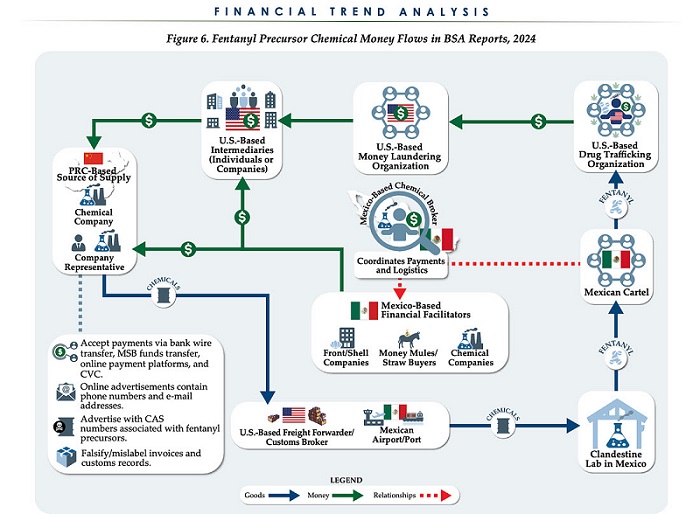
The U.S. Treasury’s Financial Crimes Enforcement Network (FinCEN) has identified $1.4 billion in fentanyl-linked suspicious transactions, naming China, Mexico, Canada, and India as key foreign touchpoints in the global production and laundering network. The analysis, based on 1,246 Bank Secrecy Act filings submitted in 2024, tracks financial activity spanning chemical purchases, trafficking logistics, and international money laundering operations.
The data reveals that Mexico and the People’s Republic of China were the two most frequently named foreign jurisdictions in financial intelligence gathered by FinCEN. Most of the flagged transactions originated in U.S. cities, the report notes, due to the “domestic nature” of Bank Secrecy Act data collection. Among foreign jurisdictions, Mexico, China, Hong Kong, and Canada were cited most often in fentanyl-related financial activity.
The FinCEN report points to Mexico as the epicenter of illicit fentanyl production, with Mexican cartels importing precursor chemicals from China and laundering proceeds through complex financial routes involving U.S., Canadian, and Hong Kong-based actors.
The findings also align with testimony from U.S. and Canadian law enforcement veterans who have told The Bureau that Chinese state-linked actors sit atop a decentralized but industrialized global fentanyl economy—supplying precursors, pill presses, and financing tools that rely on trade-based money laundering and professional money brokers operating across North America.
“Filers also identified PRC-based subjects in reported money laundering activity, including suspected trade-based money laundering schemes that leveraged the Chinese export sector,” the report says.
A point emphasized by Canadian and U.S. experts—including former U.S. State Department investigator Dr. David Asher—that professional Chinese money laundering networks operating in North America are significantly commanded by Chinese Communist Party–linked Triad bosses based in Ontario and British Columbia—is not explored in detail in this particular FinCEN report.¹
Chinese chemical manufacturers—primarily based in Guangdong, Zhejiang, and Hebei provinces—were repeatedly cited for selling fentanyl precursors via wire transfers and money service businesses. These sales were often facilitated through e-commerce platforms, suggesting that China’s global retail footprint conceals a lethal underground market—one that ultimately fuels a North American public health crisis. In many cases, the logistics were sophisticated: some Chinese companies even offered delivery guarantees and customs clearance for precursor shipments, raising red flags for enforcement officials.
While China’s industrial base dominates the global fentanyl supply chain, Mexican cartels are the next most prominent state-like actors in the ecosystem—but the report emphasizes that Canada and India are rising contributors.
“Subjects in other foreign countries—including Canada, the Dominican Republic, and India—highlight the presence of alternative suppliers of precursor chemicals and fentanyl,” the report says.
“Canada-based subjects were primarily identified by Bank Secrecy Act filers due to their suspected involvement in drug trafficking organizations allegedly sourcing fentanyl and other drugs from traditional drug source countries, such as Mexico,” it explains, adding that banking intelligence “identified activity indicative of Canada-based individuals and companies purchasing precursor chemicals and laboratory equipment that may be related to the synthesis of fentanyl in Canada. Canada-based subjects were primarily reported with addresses in the provinces of British Columbia and Ontario.”
FinCEN also flagged activity from Hong Kong-based shell companies—often subsidiaries or intermediaries for Chinese chemical exporters. These entities were used to obscure the PRC’s role in transactions and to move funds through U.S.-linked bank corridors.
Breaking down the fascinating and deadly world of Chinese underground banking used to move fentanyl profits from American cities back to producers, the report explains how Chinese nationals in North America are quietly enlisted to move large volumes of cash across borders—without ever triggering traditional wire transfers.
These networks, formally known as Chinese Money Laundering Organizations (CMLOs), operate within a global underground banking system that uses “mirror transfers.” In this system, a Chinese citizen with renminbi in China pays a local broker, while the U.S. dollar equivalent is handed over—often in cash—to a recipient in cities like Los Angeles or New York who may have no connection to the original Chinese depositor aside from their role in the laundering network. The renminbi, meanwhile, is used inside China to purchase goods such as electronics, which are then exported to Mexico and delivered to cartel-linked recipients.
FinCEN reports that US-based money couriers—often Chinese visa holders—were observed depositing large amounts of cash into bank accounts linked to everyday storefront businesses, including nail salons and restaurants. Some of the cash was then used to purchase cashier’s checks, a common method used to obscure the origin and destination of the funds. To banks, the activity might initially appear consistent with a legitimate business. However, modern AI-powered transaction monitoring systems are increasingly capable of flagging unusual patterns—such as small businesses conducting large or repetitive transfers that appear disproportionate to their stated operations.
On the Mexican side, nearly one-third of reports named subjects located in Sinaloa and Jalisco, regions long controlled by the Sinaloa Cartel and Cartel Jalisco Nueva Generación. Individuals in these states were often cited as recipients of wire transfers from U.S.-based senders suspected of repatriating drug proceeds. Others were flagged as originators of payments to Chinese chemical suppliers, raising alarms about front companies and brokers operating under false pretenses.
The report outlines multiple cases where Mexican chemical brokers used generic payment descriptions such as “goods” or “services” to mask wire transfers to China. Some of these transactions passed through U.S.-based intermediaries, including firms owned by Chinese nationals. These shell companies were often registered in unrelated sectors—like marketing, construction, or hardware—and exhibited red flags such as long dormancy followed by sudden spikes in large transactions.
Within the United States, California, Florida, and New York were most commonly identified in fentanyl-related financial filings. These locations serve as key hubs for distribution and as collection points for laundering proceeds. Cash deposits and peer-to-peer payment platforms were the most cited methods for fentanyl-linked transactions, appearing in 54 percent and 51 percent of filings, respectively.
A significant number of flagged transactions included slang terms and emojis—such as “blues,” “ills,” or blue dots—in memo fields. Structured cash deposits were commonly made across multiple branches or ATMs, often linked to otherwise legitimate businesses such as restaurants, salons, and trucking firms.
FinCEN also tracked a growing number of trade-based laundering schemes, in which proceeds from fentanyl sales were used to buy electronics and vaping devices. In one case, U.S.-based companies owned by Chinese nationals made outbound payments to Chinese manufacturers, using funds pooled from retail accounts and shell companies. These goods were then shipped to Mexico, closing the laundering loop.
Another key laundering method involved cryptocurrency. Nearly 10 percent of all fentanyl-related reports involved virtual currency, with Bitcoin the most commonly cited, followed by Ethereum and Litecoin. FinCEN flagged twenty darknet marketplaces as suspected hubs for fentanyl distribution and cited failures by some digital asset platforms to catch red-flag activity.
Overall, FinCEN warns that fentanyl-linked funds continue to enter the U.S. financial system through loosely regulated or poorly monitored channels, even as law enforcement ramps up enforcement. The Drug Enforcement Administration reported seizures of over 55 million counterfeit fentanyl pills in 2024 alone.
The broader pattern is unmistakable: precursor chemicals flow from China, manufacturing occurs in Mexico, Canada plays an increasing role in chemical acquisition and potential synthesis, and drugs and proceeds flood into the United States, supported by global financial tools and trade structures. The same infrastructure that enables lawful commerce is being manipulated to sustain the deadliest synthetic drug crisis in modern history.
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
Invite your friends and earn rewards
-

 2025 Federal Election12 hours ago
2025 Federal Election12 hours agoThe Federal Brief That Should Sink Carney
-
 2025 Federal Election14 hours ago
2025 Federal Election14 hours agoHow Canada’s Mainstream Media Lost the Public Trust
-

 2025 Federal Election17 hours ago
2025 Federal Election17 hours agoOttawa Confirms China interfering with 2025 federal election: Beijing Seeks to Block Joe Tay’s Election
-
 2025 Federal Election16 hours ago
2025 Federal Election16 hours agoReal Homes vs. Modular Shoeboxes: The Housing Battle Between Poilievre and Carney
-
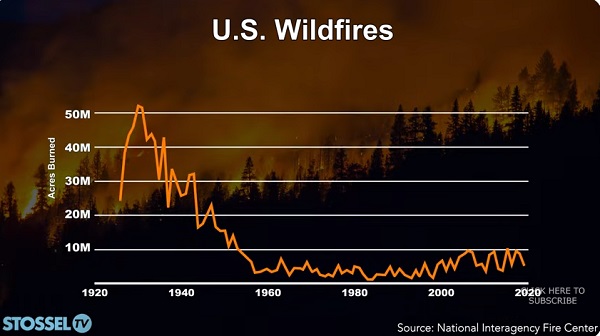
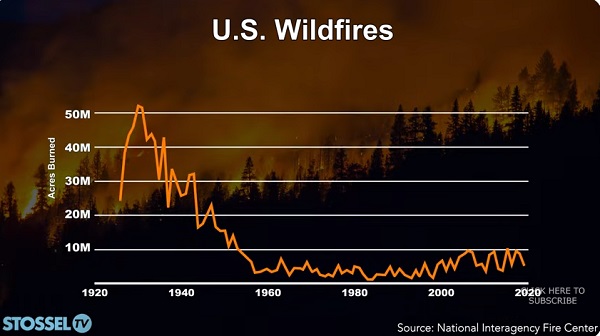 John Stossel13 hours ago
John Stossel13 hours agoClimate Change Myths Part 2: Wildfires, Drought, Rising Sea Level, and Coral Reefs
-

 COVID-1915 hours ago
COVID-1915 hours agoNearly Half of “COVID-19 Deaths” Were Not Due to COVID-19 – Scientific Reports Journal
-

 2025 Federal Election2 days ago
2025 Federal Election2 days agoPoilievre Campaigning To Build A Canadian Economic Fortress
-

 Entertainment2 days ago
Entertainment2 days agoPedro Pascal launches attack on J.K. Rowling over biological sex views


