Censorship Industrial Complex
Trudeau’s new online censorship law – Problems with Bill C-63 / the Online Arms Law

From the Canadian Constitution Foundation
Proposed Online Harms Act (Bill C-63) described by the Canadian Constitution Foundation
The Trudeau government has proposed a new law to regulate the internet, and it has major constitutional problems.
The Online Harms Act would limit constitutionally-protected expression in the following ways:
– The Bill would create a new process for individuals and groups to complain to the Canadian Human Rights Commission that online speech directed at them is discriminatory. The tribunal could order fines of up to $50,000, and awards of up to $20,000 paid to complainants, who in some cases would be anonymous. Findings would be based on a mere “balance of probabilities” standard rather than the criminal standard of proof beyond a reasonable doubt.
– The subjectivity of defining “hate speech” will lead to punishments for protected speech. The mere threat of human rights complaints will chill large amounts of protected speech.
– The Bill would increase the maximum sentence for “advocating genocide” from five years in prison to life in prison. That means words alone could lead to life imprisonment.
– The Bill would allow judges to put prior restraints on people who they believe on reasonable grounds may commit speech crimes in the future. The accused would be forced to choose between imprisonment or a “recognizance to keep the peace” that may be accompanied by severe conditions such as giving a bodily sample, refraining from drugs and alcohol, giving up firearms and wearing an ankle monitor.
– The Bill would require social media companies to “minimize the risk that users of the service will be exposed to harmful content” with the threat of massive fines if they don’t properly mitigate the risk. Social media companies will likely err on the side of caution and block large amounts of speech that is close to the legal line.
– The Bill would require social media companies to provide a mechanism for users to flag content that they believe is “harmful content,” which is defined as including speech that “foments hatred.” This will inevitably lead to censorship of legally-protected speech.
– The Bill would require social media companies to report on how they dealt with perfectly legal but otherwise “harmful content” that “the operator had reasonable grounds to believe posed a risk of significant psychological or physical harm.” This appears aimed at encouraging social media companies to censor speech that the government cannot outlaw.
In this episode I mention a tweet thread by my colleague Josh Dehaas. You can read it here:  / 1762510237032951848
/ 1762510237032951848
I also mention an op-ed by my colleague Joanna Baron. You can read it here: https://thehub.ca/2024-02-28/joanna-b…
I also talk about two important Supreme Court cases about hate speech. You can read those cases here: https://scc-csc.lexum.com/scc-csc/scc… https://scc-csc.lexum.com/scc-csc/scc…
Please write to your MP to express your concerns about this law using this online portal we created: https://theccf.ca/fix-c-63/
Censorship Industrial Complex
Canadian pro-freedom group sounds alarm over Liberal plans to revive internet censorship bill
From LifeSiteNews
The Democracy Fund warned that the Liberal government may bring back a form of Bill C-63, which is aimed at regulating online speech.
One of Canada’s top pro-democracy groups has sounded the alarm by warning that the Canadian federal government is planning to revive a controversial Trudeau-era internet censorship bill that lapsed.
The Democracy Fund (TDF), in a recent press release, warned about plans by the Liberal government under Prime Minister Mark Carney to bring back a form of Bill C-63. The bill, which lapsed when the election was called earlier this year, aimed to regulate online speech, which could mean “mass censorship” of the internet.
“TDF is concerned that the government will try once more to give itself the power to criminalize and punish online speech and debate,” the group said.
“TDF will oppose that.”
According to the TDF, it is “concerned that the government intends to re-introduce the previously abandoned Online Harms Bill in the same or modified form.”
Bill C-63, or the Online Harms Act, was put forth under the guise of protecting children from exploitation online. The bill died earlier this year after former Prime Minister Justin Trudeau called the 2025 federal election.
While protecting children is indeed a duty of the state, the bill included several measures that targeted vaguely defined “hate speech” infractions involving race, gender, and religion, among other categories. The proposal was thus blasted by many legal experts.
The Online Harms Act would have censored legal internet content that the government thought “likely to foment detestation or vilification of an individual or group.” It would be up to the Canadian Human Rights Commission to investigate complaints.
The TDF said that Bill C-63 would have made it a criminal offense to publish ill-defined “harmful content.”
“It required social media companies to remove potentially harmful content or face punitive fines. Many defenders of civil liberty, including TDF, worried that the application of this badly defined concept would lead to mass surveillance and censorship,” the group said.
The TDF warned that under Carney, the government is “once again considering new or similar legislation to regulate online speech, with the Minister of Justice claiming he would take another look at the matter.”
Mark Joseph, TDF litigation director, pointed out that Canada already has laws that “the government can, and does, use to address most of the bad conduct that the Bill ostensibly targeted.”
“To the extent that there are gaps in the Criminal Code, amendments should be carefully drafted to fix this,” he said.
“However, the previous Bill C-63 sought to implement a regime of mass censorship.”
As reported by LifeSiteNews last month, a recent Trudeau-appointed Canadian senator said that he and other “interested senators” want Carney to revive a controversial Trudeau-era internet censorship bill that lapsed.
Another recent Carney government Bill C-2, which looks to ban cash donations over $10,000, was blasted by a constitutional freedom group as a “step towards tyranny.”
Carney, as reported by LifeSiteNews, vowed to continue in Trudeau’s footsteps, promising even more legislation to crack down on lawful internet content.
He has also said his government plans to launch a “new economy” in Canada that will involve “deepening” ties to the world.
Under Carney, the Liberals are expected to continue much of what they did under Justin Trudeau, including the party’s zealous push in favor of abortion, euthanasia, radical gender ideology, internet regulation and so-called “climate change” policies. Indeed, Carney, like Trudeau, seems to have extensive ties to both China and the globalist World Economic Forum, connections that were brought up routinely by conservatives in the lead-up to the election.
Censorship Industrial Complex
Global media alliance colluded with foreign nations to crush free speech in America: House report

From LifeSiteNews
By Dan Frieth
The now-defunct ad coalition GARM shared insider data and urged boycotts of Twitter to punish non-compliance with its ‘harmful content’ standards, a US House Judiciary report shows.
A new report from the U.S. House Judiciary Committee has shed light on what it describes as an alarming collaboration between powerful corporations and foreign governments aimed at suppressing lawful American speech.
The investigation focuses on the Global Alliance for Responsible Media (GARM), an initiative founded in 2019 by the World Federation of Advertisers (WFA), which the committee accuses of acting as a censorship cartel.
According to the report, GARM, whose members control about 90 percent of global advertising spending, exploited its market dominance to pressure platforms like Twitter (now X) into compliance with its restrictive content policies.
A copy of the report can be found HERE.
The committee highlighted how GARM sought to “effectively reduce the availability and monetization” of content it deemed harmful, regardless of public demand for free expression.
Documents obtained by the committee reveal direct coordination between GARM and foreign regulators, including the European Commission and Australia’s eSafety commissioner.
In one exchange, a European bureaucrat encouraged advertisers to leverage their influence to “push Twitter to deliver on GARM asks.”

Similarly, Australia’s eSafety Commissioner Julie Inman Grant praised GARM’s “significant collective power in helping to hold the platforms to account” and sought updates to “take into account in our engagement and regulatory decisions.”

Robert Rakowitz, GARM’s co-founder and initiative lead, expressed a chilling goal in private correspondence, stating that silencing President Donald Trump was his “main thing” and likening the president’s speech to a “contagion” he aimed to contain “to protect infection overall.”

The report outlines how GARM distributed previously unavailable non-public information about Twitter’s adherence to its standards, fully aware this would prompt advertisers to boycott the platform if it failed to conform. According to the House report, Rakowitz admitted that this information sharing was designed to encourage members not to advertise on Twitter.
He went as far as to draft statements urging GARM members to halt advertising on the platform, telling colleagues he had gone “as close as possible” to saying Twitter “is unsafe, cease and desist.”
Despite the widespread impact of GARM’s actions, including what the committee describes as coerced “concessions” from platforms, internal polling circulated within GARM showed that “66 percent of American consumers valued free expression over protection from harmful content.”
Still, GARM pressed ahead with efforts to “eliminate all categories of harmful content in the fastest possible timing,” ignoring consumer preferences.
Even after GARM dissolved in 2024 amid legal challenges, similar efforts persisted.
A new coalition led by Dentsu and The 614 Group briefly attempted to revive GARM’s mission before disbanding under scrutiny. Gerry D’Angelo, a former GARM leader, reflected on the initiative’s overreach, stating, “Did we go too far in those first rounds of exclusionary restrictions? I would say yes.”
The Judiciary Committee warns that despite GARM’s downfall, the threat of collusion to stifle free expression remains.
It pledged to continue oversight to defend “the fundamental principles” of the Constitution and ensure that markets, not coordinated censorship efforts, shape the flow of information in the digital age.
Reprinted with permission from Reclaim The Net.
-

 MAiD2 days ago
MAiD2 days agoCanada’s euthanasia regime is already killing the disabled. It’s about to get worse
-

 Daily Caller16 hours ago
Daily Caller16 hours agoUSAID Quietly Sent Thousands Of Viruses To Chinese Military-Linked Biolab
-
 Alberta13 hours ago
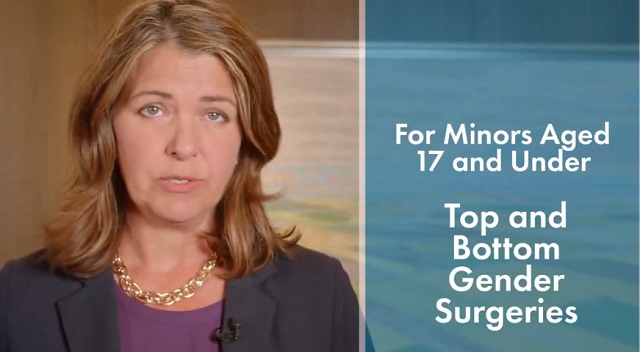
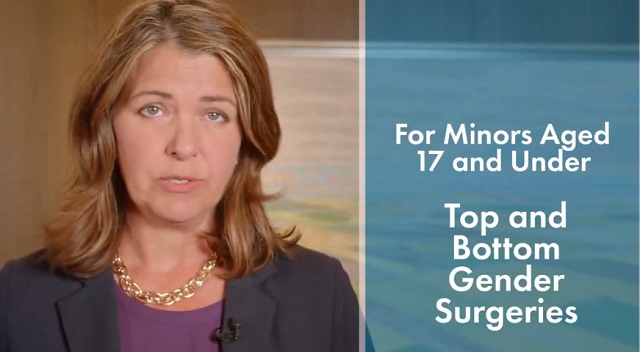
Alberta13 hours ago‘Far too serious for such uninformed, careless journalism’: Complaint filed against Globe and Mail article challenging Alberta’s gender surgery law
-
 Censorship Industrial Complex24 hours ago
Censorship Industrial Complex24 hours agoCanadian pro-freedom group sounds alarm over Liberal plans to revive internet censorship bill
-

 Fraser Institute1 day ago
Fraser Institute1 day agoBefore Trudeau average annual immigration was 617,800. Under Trudeau number skyrocketted to 1.4 million from 2016 to 2024
-

 International2 days ago
International2 days agoChicago suburb purchases childhood home of Pope Leo XIV
-
 Daily Caller2 days ago
Daily Caller2 days ago‘I Know How These People Operate’: Fmr CIA Officer Calls BS On FBI’s New Epstein Intel
-

 Economy1 day ago
Economy1 day agoThe stars are aligning for a new pipeline to the West Coast

