Crime
RCMP Bust B.C. Fentanyl Superlab Linked to Mexico and Transnational Exports

In a remote mountainous area of British Columbia, federal police have dismantled the largest fentanyl laboratory ever discovered in Canada. This western province has become a critical front in the Five Eyes battle against the production and distribution of deadly synthetic narcotics trafficked globally by networks involving Chinese and Iranian state-sponsored mafias and Mexican cartels.
In a groundbreaking discovery, the RCMP located the superlab in Falkland—a village of 946 residents nestled in the rugged terrain between Calgary and Vancouver—using Phenyl-2-Propanone (P2P) to manufacture methamphetamine. This production method, primarily employed by Mexican cartels, stems from the precursors and scientific expertise Mexican cartels have gathered from elite Chinese criminals since the early 2000s, according to U.S. enforcement sources.
David Teboul, Commander of the RCMP Federal Policing program in the Pacific Region, underscored the significance: “Manufacturing methamphetamine using P2P had not been seen in Western Canada until now,” he said. “The P2P manufacturing method has been the primary method used by Mexican cartels to produce methamphetamine for years.”
Demonstrating the destructive power of the cartels involved, the RCMP seized a staggering cache of illicit substances and weapons. Officers confiscated 54 kilograms of fentanyl, massive amounts of precursor chemicals, 390 kilograms of methamphetamine, 35 kilograms of cocaine, 15 kilograms of MDMA, and 6 kilograms of cannabis. The superlab was described as the largest and most sophisticated of its kind, capable of producing multiple types of illicit drugs.
“To put things into context,” Teboul said, “the over 95 million potentially lethal doses of fentanyl that have been seized could have taken the lives of every Canadian at least twice over.”
A large portion of the product was destined for other countries.
During the investigation, RCMP officers learned of several large shipments of methamphetamine prepared for international export. They intercepted 310 kilograms of methamphetamine before it could leave Canada, preventing a significant quantity from reaching global markets—a critical point as Canada faces pressure from its allies over its role in the global fentanyl and methamphetamine trade.
Teboul noted that the RCMP collaborated with its Five Eyes enforcement partners—an intelligence alliance comprising Canada, the United States, the United Kingdom, Australia, and New Zealand. Although Teboul did not provide specific details, this cooperation underscores the international scope of the transnational investigation.
The first suspect, Gaganpreet Singh Randhawa, was identified and arrested during raids. He is currently in custody and faces multiple charges, including possession and export of controlled substances, possession of prohibited firearms and devices, and possession of explosive devices. More arrests are expected, Teboul said.
The scale of this criminal network echoes the power and violence fueling gang wars that have rocked British Columbia, putting innocent lives at risk during high-powered shootouts in Vancouver. Investigators seized a total of 89 firearms, including 45 handguns, 21 AR-15-style rifles, and submachine guns—many of which were loaded and ready for use. The searches also uncovered small explosive devices, vast amounts of ammunition, firearm silencers, high-capacity magazines, body armor, and $500,000 in cash.
British Columbia has been grappling with an influx of synthetic opioids like fentanyl, significantly exacerbating the opioid crisis across Canada. The province has witnessed a surge in overdose deaths, prompting law enforcement to intensify efforts against drug production and trafficking networks. Experts highlight weaknesses in Canadian laws and a lack of federal oversight at the Port of Vancouver, which have been exploited by transnational crime and money laundering organizations from China, Iran, and Mexico.
This significant bust comes at a time when Canada is under increased scrutiny from international allies over its role as a hub for the export of fentanyl and methamphetamine. The superlab takedown appears to align with serious concerns raised by lawmakers in Washington about how Canada and Mexico are being used by transnational crime organizations to distribute fentanyl worldwide.
A recent U.S. congressional report argues that the Chinese Communist Party’s (CCP) strategy relies less on overt military actions and more on covert tactics, including trafficking of fentanyl and leveraging money laundering, aimed at exploiting vulnerabilities across social, economic, and health domains.
“Fentanyl precursors are manufactured in China and shipped to Mexico and Canada. For precursors that arrive in Mexico, Chinese transnational mafias work with Mexican cartels to smuggle and distribute fentanyl in the United States on behalf of the CCP,” the report states. “The DEA confirmed Chinese transnational crime leaders hold government positions in the CCP and indicated that Chinese transnational crime organizations are dedicated to the CCP.”
“The public deserves to know about the CCP’s role in fentanyl production and how the Party is using fentanyl as a chemical weapon to kill Americans,” the report adds. It recommends that Washington publicly “blame the CCP as much as the DEA and its partners currently blame the Sinaloa Cartel” for fentanyl trafficking and urges the government to “educate international allies about CCP chemical warfare” and encourage them to condemn Chinese transnational crime.
According to congressional investigations, Beijing is actively incentivizing the export of fentanyl and methamphetamine worldwide. The report alleges that Chinese criminal organizations, including Triads led by individuals with official positions in the CCP, are working alongside Mexican cartels to generate profit to fund interference operations in America.
The Bureau is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.
Crime
U.S. seizes Cuba-bound ship with illicit Iranian oil history

President Trump revealed Wednesday afternoon that U.S. authorities intercepted a Cuba-bound oil tanker off the Venezuelan coast, a dramatic move aimed at tightening the squeeze on illicit oil networks operating throughout the region. Speaking to reporters at the White House, Trump described the vessel as “a very large tanker — the largest one ever seized in action,” hinting that more developments are coming. He declined to get into specifics, saying only that the operation happened “for a very good reason.” When asked about the tanker’s crude, Trump didn’t overcomplicate it. “Well, we keep it, I guess,” he said.
According to a U.S. official familiar with the operation, the seizure was executed by the Coast Guard with support from the U.S. Navy after a federal judge green-lit the warrant roughly two weeks ago. Another official told the New York Times the ship — identified as the Skipper — had been sailing under a falsified flag and has a documented history of trafficking illicit Iranian oil. The vessel, although carrying Venezuelan crude at the time, was seized because of those Iranian smuggling ties, not because of any direct connection to Nicolás Maduro’s regime.
Today, the Federal Bureau of Investigation, Homeland Security Investigations, and the United States Coast Guard, with support from the Department of War, executed a seizure warrant for a crude oil tanker used to transport sanctioned oil from Venezuela and Iran. For multiple… pic.twitter.com/dNr0oAGl5x
— Attorney General Pamela Bondi (@AGPamBondi) December 10, 2025
Vanguard, a UK-based maritime risk firm, confirmed Wednesday that the Skipper fits the profile of a tanker previously sanctioned by the United States for operating under the alias Adisa while moving banned Iranian oil. A source speaking to Politico said the ship was on its way to Cuba, where state-run Cubametales intended to flip the cargo to Asian brokers — an increasingly common workaround as U.S. sanctions isolate both Havana and Caracas from traditional buyers. With most Venezuelan product now flowing to China under the sanctions regime, oil traders began recalibrating almost immediately after the news broke. Prices ticked upward modestly as markets waited to learn whether any Venezuelan crude was on board and how much would be effectively taken off the table.
Maduro, for his part, avoided directly mentioning the seizure during a speech later Wednesday, instead railing against the United States and claiming Venezuela’s military stands ready “to break the teeth of the North American empire, if necessary.” His bluster did little to obscure the reality: the Trump administration just disrupted yet another shadowy oil operation linking Caracas, Havana, and Tehran — and sent a clear signal that these networks will be confronted, tanker by tanker.
Crime
Inside the Fortified Sinaloa-Linked Compound Canada Still Can’t Seize After 12 Years of Legal War

Exclusive analysis shows how a fortified Surrey mansion tied in court filings to the Sinaloa Cartel’s leader has become the core of a stalled civil forfeiture fight, exposing Canada’s weak laws.
A British Columbia government lawsuit seeks to merge almost a decade of litigation into a single, high-stakes test of whether the province can finally seize a fortified mansion near the U.S. border that was first swept up in a 2014 fentanyl investigation, raided in 2016, and is now at the center of a new synthetic-opioid case alleging its occupants contracted with the leader of Mexico’s Sinaloa Cartel to flood narcotics into Canada.
In a notice of application filed in November 2025, the Director of Civil Forfeiture argues that all of the files revolve around one owner — James Sydney Sclater — and his flagship property on 77th Avenue, a multi-million-dollar house about twenty minutes’ drive from the Peace Arch crossing.
The property became newly notorious this spring when the latest effort to seize it pulled back the curtain on a 2024 RCMP raid. Officers say they entered a mansion ringed by compound fencing, steel gates and razor wire, wired with Chinese-made Hikvision surveillance cameras and hardened doors.
Inside, they reported finding hidden compartments in bedrooms and a basement bathroom packed with counterfeit pills and kilograms of raw synthetic opioids — including fentanyl — while assault-style rifles with screw-on suppressors, thousands of bullets and other firearms and body armour were stored in ways that suggested the residents were prepared for urban warfare. Investigators later alleged the targets had “connections to virtually every criminal gang in British Columbia.”
They also seized travel documents, including Mexican visas, before tracing the operation to alleged negotiations with Ismael “El Mayo” Zambada García, the reputed head of the Sinaloa Cartel, which Ottawa has now listed as a terrorist entity.
But for Canadian anti-mafia units, the address tracks the history of fentanyl’s deadly sweep across British Columbia, among the hardest-hit opioid death zones in North America. Their interest in the Surrey mansion stretches back to the first wave of lethal fentanyl trafficking that surged from Vancouver’s Downtown Eastside to Victoria and Vancouver Island around 2013 — making this single property a through-line in the North American opioid crisis, one that now runs through senior offices in Washington, Mexico City, Beijing and Ottawa.
Behind the hundreds of pages of civil filings reviewed by The Bureau lies a failure of governance as urgent as the unchecked advance of Latin cartels into Canadian cities — and as lethal as the synthetic opioids tied to the Surrey home.
British Columbia has been chasing the same house, and the same alleged transnational traffickers, through raids, affidavits and Charter of Rights battles since before fentanyl became a household word — and still has not managed to take the keys away.
The case documents explicitly point to a criminal-defence-friendly Supreme Court of Canada ruling — Stinchcombe, notoriously cited by police leaders — and to its role in undermining numerous major prosecutions involving networks tied to alleged narcoterror suspect Ryan Wedding and modern Canadian fentanyl-lab operators. One of those networks is the Wolfpack, a hybrid of Mexican cartels, Middle Eastern threat networks and biker gangs said to be supplied by Chinese Communist Party–linked criminal organizations and other Latin American cartel interests.
For the Director, the newest chapter begins in earnest with an RCMP raid on September 23, 2024. By then, investigators say, the Surrey mansion was no longer a domestic drug base, but the Canadian end of a supply line reaching into Sinaloa itself. Notably, 38 days later, on October 31, the RCMP announced a separate raid on what U.S. sources describe as the largest fentanyl lab ever discovered in the world, in rugged Falkland, B.C., roughly halfway between Vancouver and Calgary.
“The combined fentanyl and precursors seized at this facility could have amounted to over 95,500,000 potentially lethal doses of fentanyl, which have been prevented from entering our communities, or exported abroad,” the Mounties said.
But Sinaloa does not appear out of nowhere in the Surrey compound. The older case that the Director now wants consolidated onto the same track reaches back to a different phase of the crisis — and sketches an earlier incarnation of the Surrey house as a node in a Lower Mainland fentanyl network.
According to a 2019 notice of civil claim filed in the Victoria registry, the RCMP’s Project E-Probang began in November 2014, targeting a chemical narcotics distribution network that operated across the Lower Mainland and Vancouver Island. At the centre of that probe, police say, was Nicholas Lucier and his associates. The Director alleges that Sclater supplied Lucier’s network with controlled substances, while his father-in-law Gary Van Buuren lived with him at the 77th Avenue property and “assisted him in trafficking of controlled substances.”
The narrative that follows reads like a blueprint for mid-2010s fentanyl tradecraft. In October 2016, Lucier associate Yevgeniy Nagornyy-Kryvonos allegedly drove to the Surrey mansion to receive fentanyl from Sclater. Two days later, Nagornyy-Kryvonos met Daemon Gariepy; Gariepy was arrested shortly after that meeting, with one kilogram of fentanyl in his possession. On November 6, 2016, Sclater and Van Buuren visited the Surrey home of another associate, Azam Abdul. Van Buuren was picked up soon afterwards, allegedly carrying a kilogram of methamphetamine, a kilogram of fentanyl and two cellphones.
That same day, RCMP officers moved in on 16767 77th Avenue with a warrant. Inside, according to the pleadings, they found the kind of infrastructure that exists to supply major drug lines: long guns and improvised weapons scattered through the house, from conventional shotguns and rifles to a deactivated grenade, brass knuckles and a small armoury of knives, batons and throwing stars. There was a money counter parked near vacuum-sealing equipment; shelves of drug-packaging and currency-bundling materials; a body armour vest; and a banknote stash of roughly $20,000 in twenties, bundled with elastic bands and tucked into vacuum-sealed bags.
Fentanyl-containing pills and scoresheets documenting transactions sat alongside a multi-monitor surveillance system and a wiretap-detection kit. In a separate corner, tax records in Sclater’s name showed his declared income stepping down from more than $77,000 in 2010 to just over $11,000 by 2014 — data points that undermined his ability to carry mortgages on two Surrey properties.
The days that followed widened the picture.
A search at Abdul’s residence turned up scales, fentanyl and the tools of drug production and processing. Raids at Lucier’s home and two rentals he allegedly used produced what the Director describes as a haul worth a serious cartel’s attention: weapons and ammunition, more than $2-million in cash, and “thousands of grams” of fentanyl, cocaine, methamphetamine, a heroin-fentanyl mixture, fentanyl “oxy” tablets and MDMA, along with the scoresheets and processing gear that underpin a wholesale operation.
On Vancouver Island, an arrest search of Lucier allegedly produced tens of thousands of dollars in cash and multiple phones.
Lucier had been on Canadian police radar since at least the mid-2000s, and his story intertwines with the murder of B.C. cocaine broker Tom Gisby in Mexico — a killing that, according to a Canadian police source interviewed by The Bureau, formed part of a bloody consolidation of Mexican cartel power over Vancouver’s drug markets.
Lucier’s notoriety stretches back to October 2009, when Victoria police announced what they described as the city’s largest-ever cocaine bust. After a three-month undercover probe triggered by a shooting near Beacon Hill Park, nearly 100 officers carried out pre-dawn raids on five locations around the capital region, seizing roughly 22.5 kilograms of cocaine, four high-powered handguns, two vehicles and about $420,000 in cash. Lucier, then 41 and already on parole from a 2007 trafficking sentence involving multi-kilogram quantities of cocaine and heroin, was the lone suspect to slip away; a Canada-wide warrant was issued for his arrest.
In 2012, police in Mexico’s Nayarit state announced they had arrested Lucier in the Pacific resort city of Nuevo Vallarta on the outstanding Canadian warrant — the same town where Gisby, a longtime player in British Columbia’s cocaine trade, had been shot dead days earlier while ordering coffee at a Starbucks. Mexican authorities said Lucier had been living under an assumed name and socializing with other Canadian expatriates in the Puerto Vallarta area, including people who knew Gisby, although his arrest was not believed to be directly tied to the murder.
For investigators, the episode underscored how Canadian traffickers were deeply embedded in Mexican resort corridors from Mazatlán to Cancún that doubled as hubs for cartel-linked players from the north. In the years that followed, it would be former Canadian snowboarder Ryan Wedding — tightly associated with the Wolfpack networks tied to Western Canada’s fentanyl superlabs — who, according to U.S. government sources, rose above other Canadian narcos in those resort towns to become perhaps the single conduit for Latin American–supplied narcotics imported into Canada for both domestic consumption and onward transshipment.
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
No Charges on Fentanyl Network
E-Probang era investigations underpin the 2019 civil claim that seeks forfeiture of both the 77th Avenue mansion and a second property at 15797 92nd Avenue. The Director’s position is that the homes were purchased and maintained with money that cannot be reconciled with Sclater’s reported earnings and should be treated as the proceeds of crime.
According to an amended notice of civil claim filed in May 2025, Sclater shared the 77th Avenue house with Hector Armando Chavez-Anchondo and John Brian Whalen, while Whalen’s father, John Edwin Whalen, and Brittany Anne Horvey are drawn into the case through their alleged roles in what the Director calls a drug trafficking organization, or DTO. The court filings describe not a loose circle of dealers, but a structured group that trafficked ketamine, methamphetamine, counterfeit Xanax, oxycodone, MDMA and fentanyl, and that “since June 2021 at the latest” had been working to import bulk cocaine from Mexico.
As the Director tells it, those efforts led straight to Sinaloa itself. The Surrey group is alleged to have agreed to purchase cocaine from senior cartel suppliers — operating at such scale, sophistication and power within Canada that they ultimately negotiated directly with alleged cartel boss Ismael “El Mayo” Zambada García.
When U.S. authorities arrested El Mayo on July 25, 2024, the Surrey operation is said to have lurched sideways, searching for “other parties” to keep the cocaine pipeline alive. In early September, Sclater, Chavez-Anchondo and Whalen Jr. allegedly pooled money to secure a shipment, then drove out to a rendezvous where they expected to collect their imported cocaine. According to the filings, their transport contact never materialized, and they returned to Surrey empty-handed.
Eleven days later, the RCMP arrived with a search warrant. Inside the mansion, officers reported walking into what looked more like a mid-level cartel outpost than a suburban home: firearms racked and stashed in multiple rooms, including assault-style rifles with screw-on suppressors and piles of ammunition, suggesting residents lived with the expectation of raids or perhaps clashes with some of the six other Mexican cartel networks aside from Sinaloa that have been identified in Canada by federal police.
Hidden compartments had been carved into bedrooms and a basement bathroom, where police say they found kilogram-scale quantities of ketamine and methamphetamine, counterfeit alprazolam tablets pressed to resemble Xanax, hundreds of oxycodone pills, a smaller but potent stash of fentanyl, and bundles of Canadian cash tucked away in a manner seasoned investigators instantly recognized — elastic-bound bricks, some vacuum-sealed, packed tightly enough to hint at far more money moving through the house than Sclater’s tax returns would ever show.
Downstairs, a kitchen freezer allegedly doubled as a storage vault for nearly a kilogram of MDMA; elsewhere, RCMP catalogued an Azure pleasure boat, a stable of trucks and custom motorcycles, gold jewellery and two Hikvision digital-video recorders that formed the core of a security system surveying the compound. The Director’s case is that neither Sclater nor his co-defendants had legitimate income capable of supporting that lifestyle, and that the house was both the proceeds and instrument of unlawful activity.
The timing was not incidental. Ottawa formally listed the Sinaloa Cartel as a terrorist entity on February 20, 2025, as one of seven Latin American criminal organizations added to Canada’s Criminal Code list in response to the fentanyl crisis and mounting U.S. pressure.
The Director’s pleadings lean into that backdrop, explicitly calling Sinaloa a terrorist entity and portraying 16767 77th Avenue as part of the infrastructure of a cartel now placed at the centre of a transnational security crisis.
While the alleged facts of police raids against the Surrey mansion seem to move steadily, the apparent lack of criminal charges against any of the targets — let alone a racketeering-style case against the network itself, which is effectively impossible to mount in Canada, where there is no U.S.-style RICO statute — reveals a litigation record that can fairly be described as broken and ineffectual, except from the perspective of criminal-defence lawyers and their clients.
The Director’s Victoria-based action was filed on May 22, 2019.
Sclater responded months later, disputing the forfeiture. In December 2019, the province produced its list of documents. Sclater replied in January 2020 with a list that named no documents at all. Over the next two years, Crown counsel sent a steady stream of letters — in March 2020, August 2021, and repeatedly between October 2021 and March 2022 — demanding a proper list and the financial and property records that would show how Sclater funded his holdings.
In a 2022 application, the Director’s frustration spilled onto the record. The submission notes that under the Civil Forfeiture Act, the core question is whether the Surrey properties are proceeds or instruments of unlawful activity — and that without basic financial disclosure, there is no way to test Sclater’s claim that they were acquired lawfully. The Director points out that documents showing income sources, mortgage servicing, and the acquisition and storage of weapons “are critical to a determination of the action on its merits,” and accuses Sclater of refusing or neglecting, for almost three years, to meet even the baseline disclosure duties imposed by the civil-procedure rules.
To head off what it casts as an attempt to turn the case into a criminal-style disclosure standoff, the Director leans on British Columbia v. PacNet Services Ltd., where the court rejected defence arguments that tried to graft the Supreme Court’s Stinchcombe-era criminal disclosure standards onto civil forfeiture proceedings. R. v. Stinchcombe — the 1991 Supreme Court of Canada decision that imposed a broad duty on the Crown to disclose all potentially relevant information so an accused can make full answer and defence under section 7 of the Charter — is firmly rooted in criminal procedure. Echoing that line of authority, the Director argues that there is “no justification” for Sclater to shelter behind Stinchcombe to avoid producing his own financial and property records, and tells the court it is “time to move [the case] forward,” with full document production or a lawful explanation for the default.
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
Constitutional Test
The newer Sinaloa-linked file adds another layer of complexity. Four of the five named defendants — Chavez-Anchondo, the two Whalens and Horvey — have not filed responses. In a separate notice of application, the Director now asks the court to treat the core allegations against them as admitted by default: that they were members of a drug trafficking organization; that they used or threatened violence; that they trafficked a catalogue of synthetic drugs and opioids; that they negotiated with Sinaloa; and that the weapons, cash and assets found in the 2024 raid are instruments and proceeds of crime.
For his part, Sclater is trying to turn the Surrey files into a constitutional test case. In his latest defence, he claims a lawful ownership interest in the 77th Avenue property, certain vehicles, cash, jewellery and electronic devices, and denies every allegation that he joined a criminal organization, conspired to import cocaine from Mexico, or negotiated with El Mayo. He acknowledges having a criminal record but disputes the particulars, and insists he had sufficient legitimate income to fund his properties and toys.
More ambitiously, he argues that the Civil Forfeiture Act itself is unconstitutional. By using allegations that he failed to declare taxable income as part of the proceeds-of-crime theory, he says, the province is encroaching on the federal government’s exclusive power over taxation under the Constitution Act, 1867. Assessing taxes owed, he points out, is the business of the Minister of National Revenue and the Tax Court of Canada. Civil forfeiture, in his view, cannot be used as a kind of shadow tax audit. He also asserts that the case “has arisen solely” from breaches of his Charter rights by RCMP officers and other state actors, arguing that the Director — “also an agent of the state” — is improperly relying on those breaches in seeking forfeiture.
It is, in effect, a bid to turn a forfeiture trial about a Surrey mansion into a referendum on how far provincial authorities can go in dismantling alleged drug networks without turning civil litigation into a criminal prosecution by another name.
All of this is unfolding against a national and continental backdrop that makes the Surrey house look less like an isolated problem than a symbol of a wider national failure.
Under National Fentanyl Sprint 2.0, Canadian police and partner agencies seized 386 kilograms of fentanyl and analogues between May 20 and October 31, 2025, with Ontario and British Columbia accounting for more than 90 per cent of that total. British Columbia reported 88 kilograms of seized fentanyl during the sprint. Yet those numbers miss some of the most alarming data points. Just days before the sprint window opened, Canada Border Services Agency officers at the Tsawwassen container facility in Delta intercepted more than 4,300 litres of chemicals from China, including 500 litres of propionyl chloride — a direct fentanyl precursor — and other substances capable of feeding clandestine labs in the Canadian wilderness for years. That shipment was destined for Calgary, and conservative estimates suggest it could have yielded enough fentanyl for billions of potentially lethal doses.
The Carney government continues to insist that Canada is primarily an end market, not a major exporter, and CBSA officials emphasize that only “small, personal doses” of finished fentanyl are being found heading south.
Seen from that angle, the fight over one Surrey mansion and the man who owns it becomes more than a story of Mexican cartels embedding in British Columbia’s wealthy suburbs.
It is a test of whether Canada’s patchwork of civil forfeiture laws, criminal prosecutions and Charter-driven disclosure rules can keep pace with transnational networks that blend Chinese chemical suppliers, Mexican cartels and domestic labs into a single system. For now, many Canadian police experts acknowledge in private — and some senior leaders flag in cautious public statements — that this test is being failed, and failed egregiously.
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
-

 National1 day ago
National1 day agoCanada’s free speech record is cracking under pressure
-

 Energy21 hours ago
Energy21 hours agoTanker ban politics leading to a reckoning for B.C.
-

 Energy22 hours ago
Energy22 hours agoMeet REEF — the massive new export engine Canadians have never heard of
-
 Business1 day ago
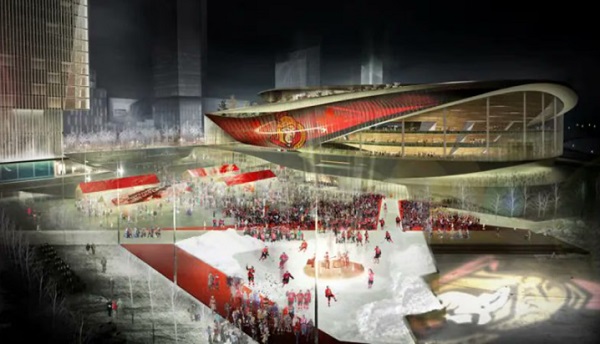
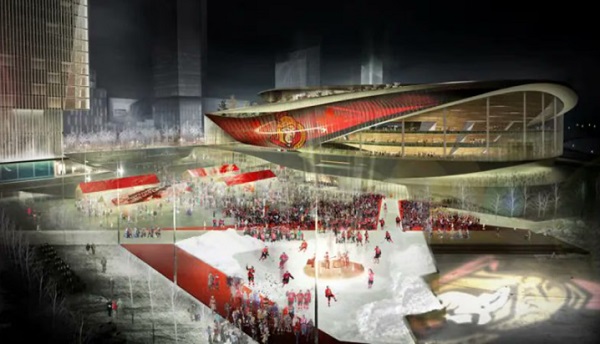
Business1 day agoTaxpayers Federation calls on politicians to reject funding for new Ottawa Senators arena
-
 Censorship Industrial Complex2 days ago
Censorship Industrial Complex2 days agoOttawa’s New Hate Law Goes Too Far
-

 Fraser Institute22 hours ago
Fraser Institute22 hours agoClaims about ‘unmarked graves’ don’t withstand scrutiny
-

 Business22 hours ago
Business22 hours agoToo nice to fight, Canada’s vulnerability in the age of authoritarian coercion
-
 Business1 day ago
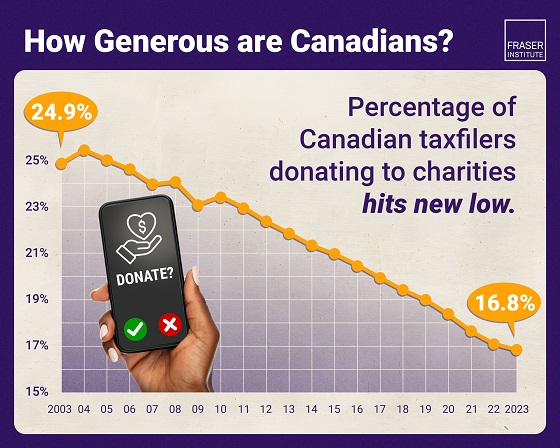
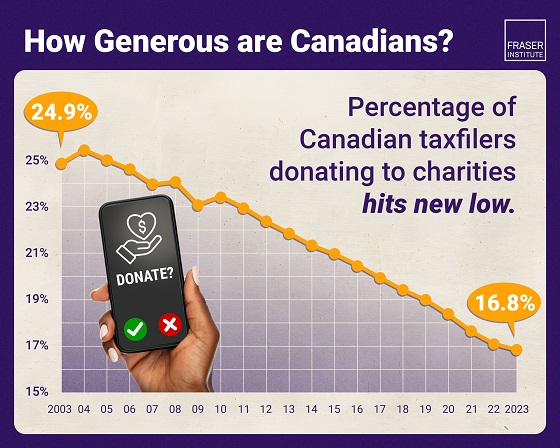
Business1 day agoAlbertans give most on average but Canadian generosity hits lowest point in 20 years






